Dr. Z's Podcasts
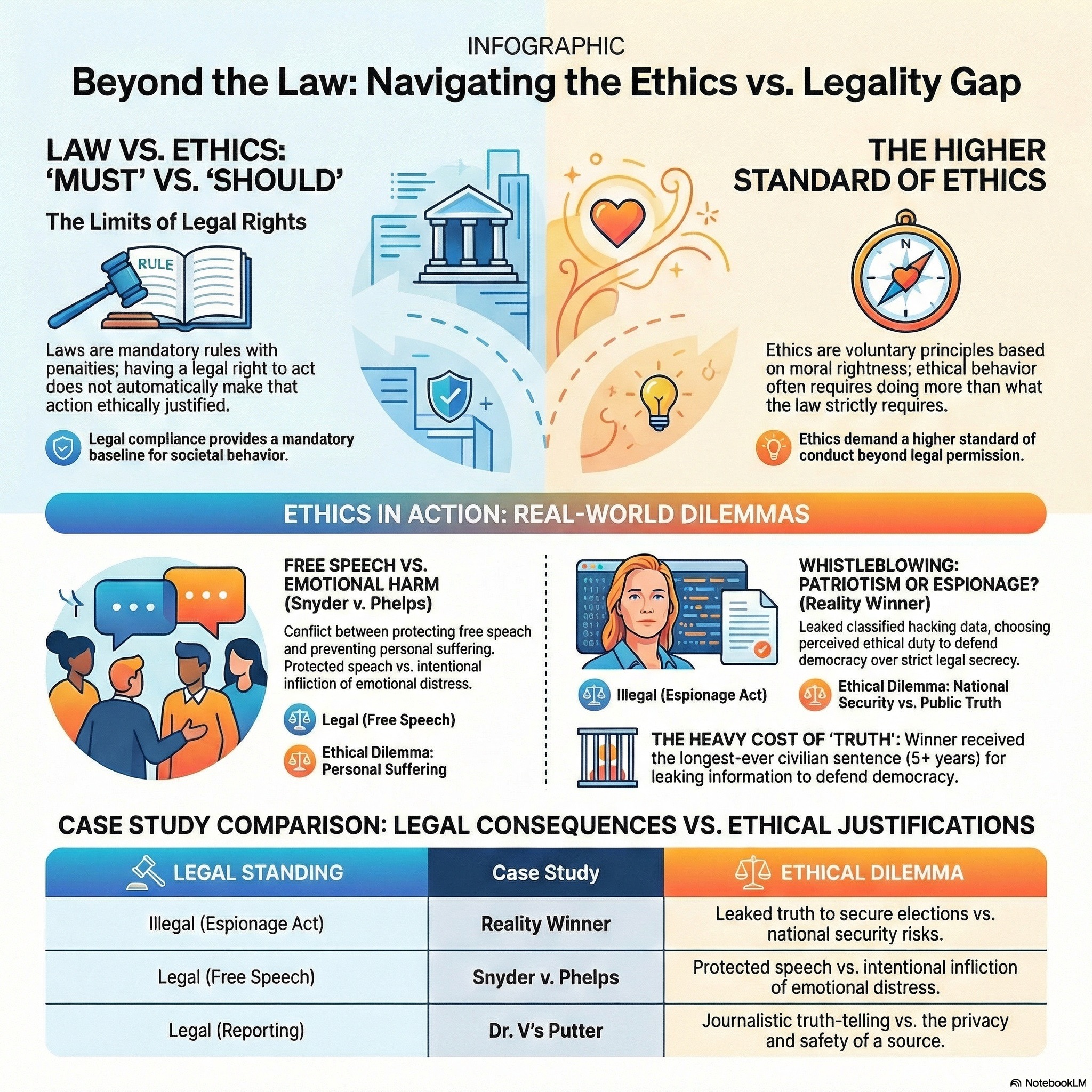
A series of podcasts to help students and everyday individuals with proper thinking and ethics. Sometimes the best decision an ethical person can make is to just stay silent, detached, and mind their own business. The podcasts include material on other courses such as security analytics and networks and security.
The Lost Art Of Traditional Western Etiquette
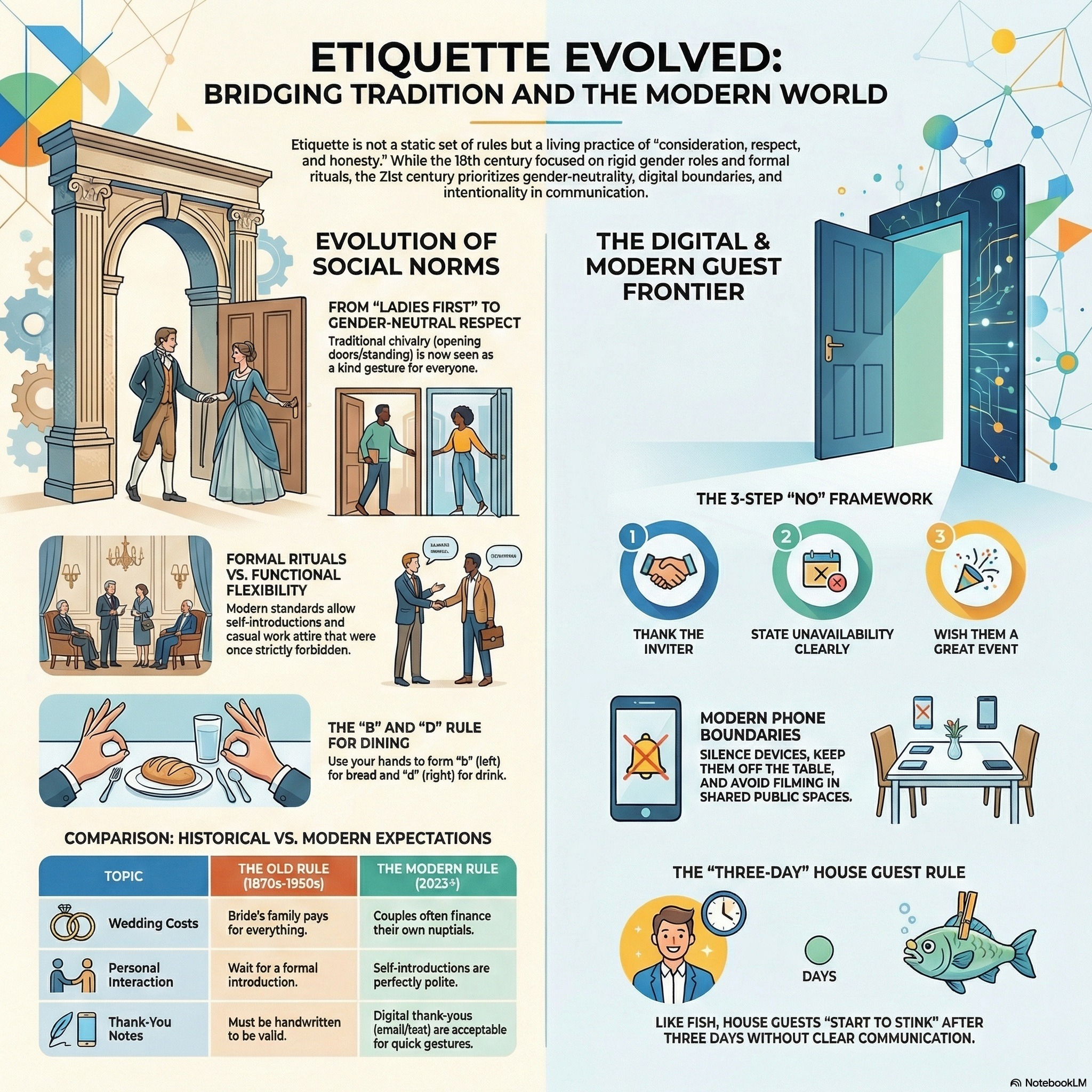
This podcast explores the evolution and application of social etiquette, ranging from historical Edwardian customs to modern digital manners. They provide practical guidance on interpersonal behavior, such as chivalrous dating acts, proper introductions based on seniority, and effective ways to politely decline invitations. A significant focus is placed on modern technology, offering specific rules for cell phone usage and navigating the complexities of American tipping culture. Additionally, the texts address lifestyle standards including professional dress codes, houseguest responsibilities, and the importance of maintaining kindness and composure in daily interactions. Overall, the collection serves as a comprehensive manual for navigating...
The Matchstick, The Hook, & The Snakes
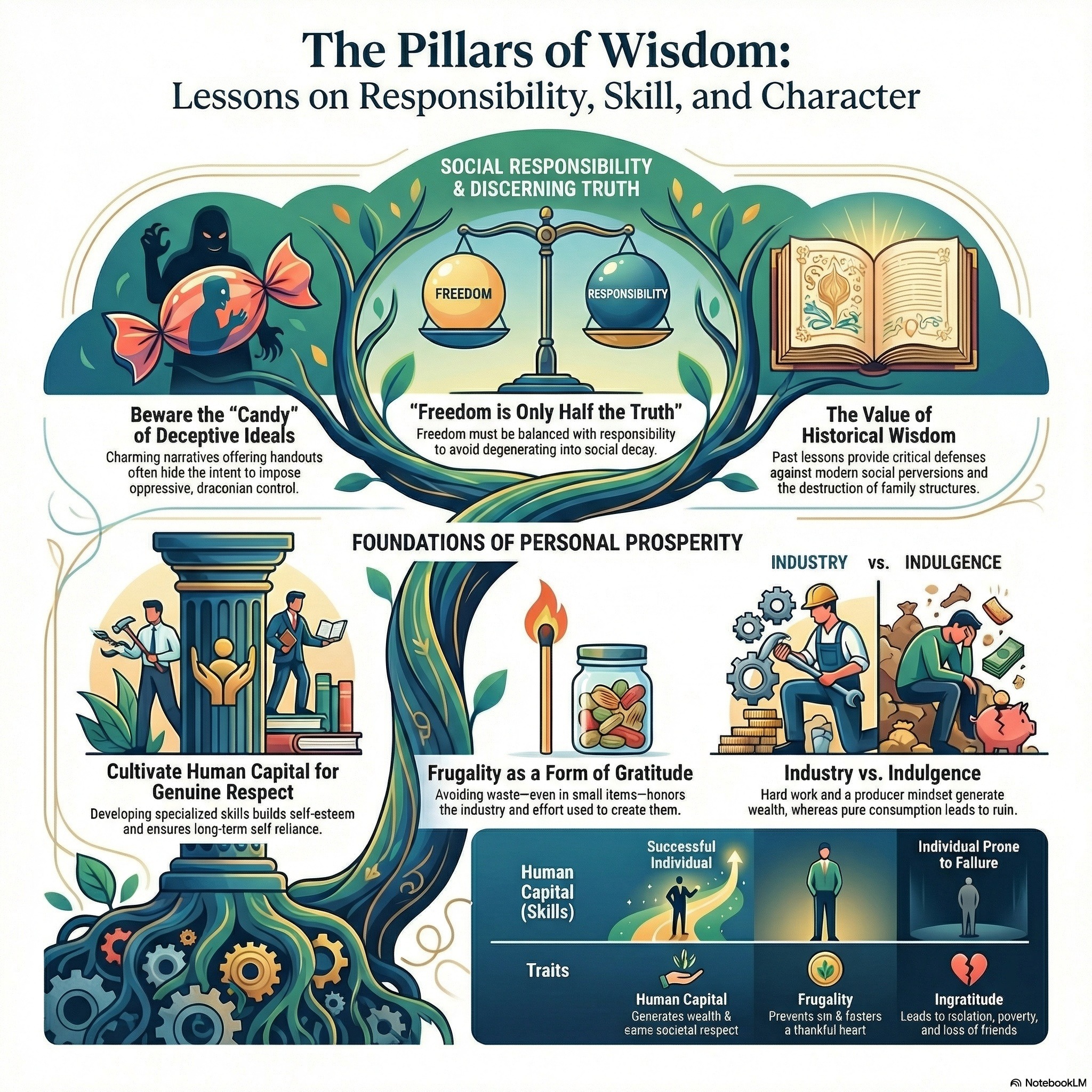
These moral fables emphasize the vital connection between personal responsibility, gratitude, and discerning wisdom. The first story illustrates how human capital and frugality are more valuable than inherited wealth, as a spoiled son only finds true purpose after losing everything and recognizing his father's foresight. In the second narrative, the consequences of gossip and the danger of freedom without accountability are explored through the manipulation of two oak trees by malicious crows. The third account warns against deceptive ideologies and the loss of liberty, using charming snakes to symbolize how societies can be hypnotized into surrendering their values. Finally...
How Intellectuals Dismantle Society From Within
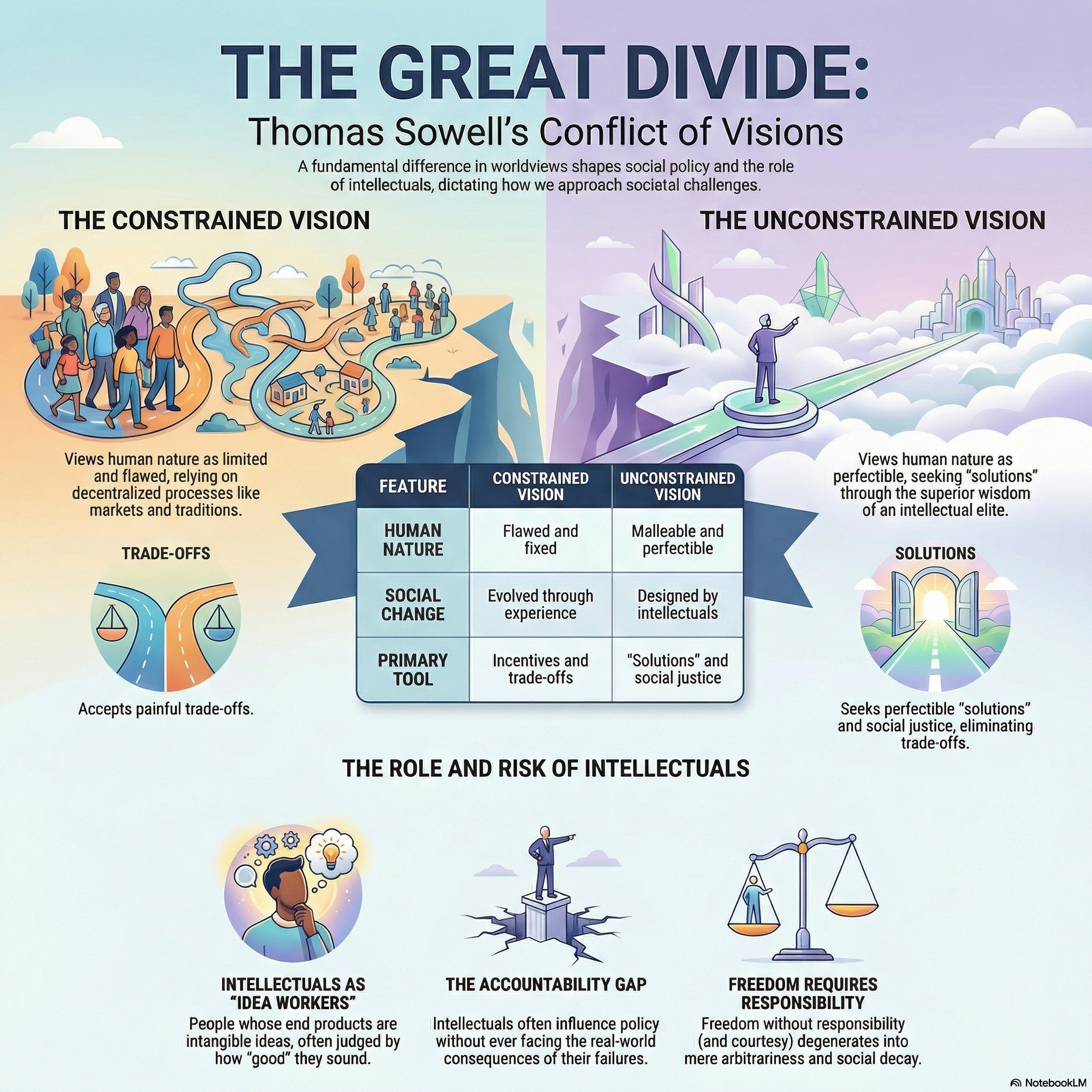
This podcast profiles the life and philosophy of Thomas Sowell, a prominent economist who critiques the "anointed" class of intellectuals for prioritizing abstract theories over empirical reality. The texts argue that modern intellectuals often champion a vision of "liberation" from traditional social restraints, which Sowell contends has historically led to disastrous outcomes like family disintegration and increased crime. Through books like Intellectuals and Society, he highlights a dangerous lack of accountability among idea workers who influence public policy without facing the consequences of their failed prescriptions. Parables within the collection further illustrate the risks of abandoning ancestral wisdom and...
Rumi’s Animals Roast Your Ego
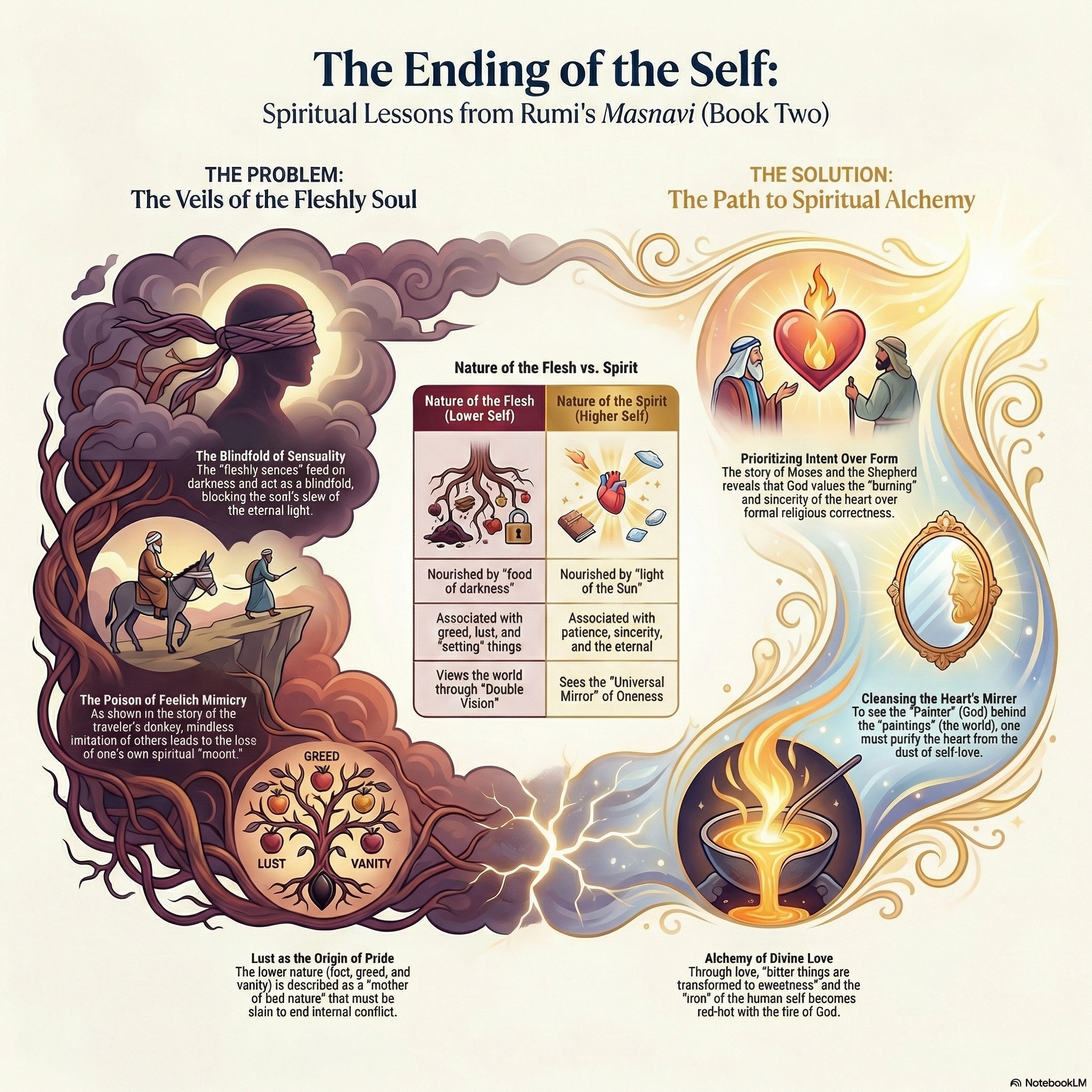
This podcast examines the mystical and pedagogical dimensions of Sufism, primarily through the symbolic Quranic narrative of Moses and the spiritual guide Khidr. Scholars and poets like Rumi and al-Qushayri use this story to illustrate the master-disciple relationship, emphasizing that true wisdom often transcends external law and human logic. The texts explore how mystical "unveiling" allows practitioners to move beyond physical senses to perceive divine realities and achieve spiritual purity. Further commentary connects these Islamic traditions to broader philosophical frameworks, including Neoplatonism and historical hagiographies of various saints. Ultimately, the collection highlights the transformation of the soul from worldly...
Ethics & Privacy - Podcast 06 - The Intellectual Property Survival Guide
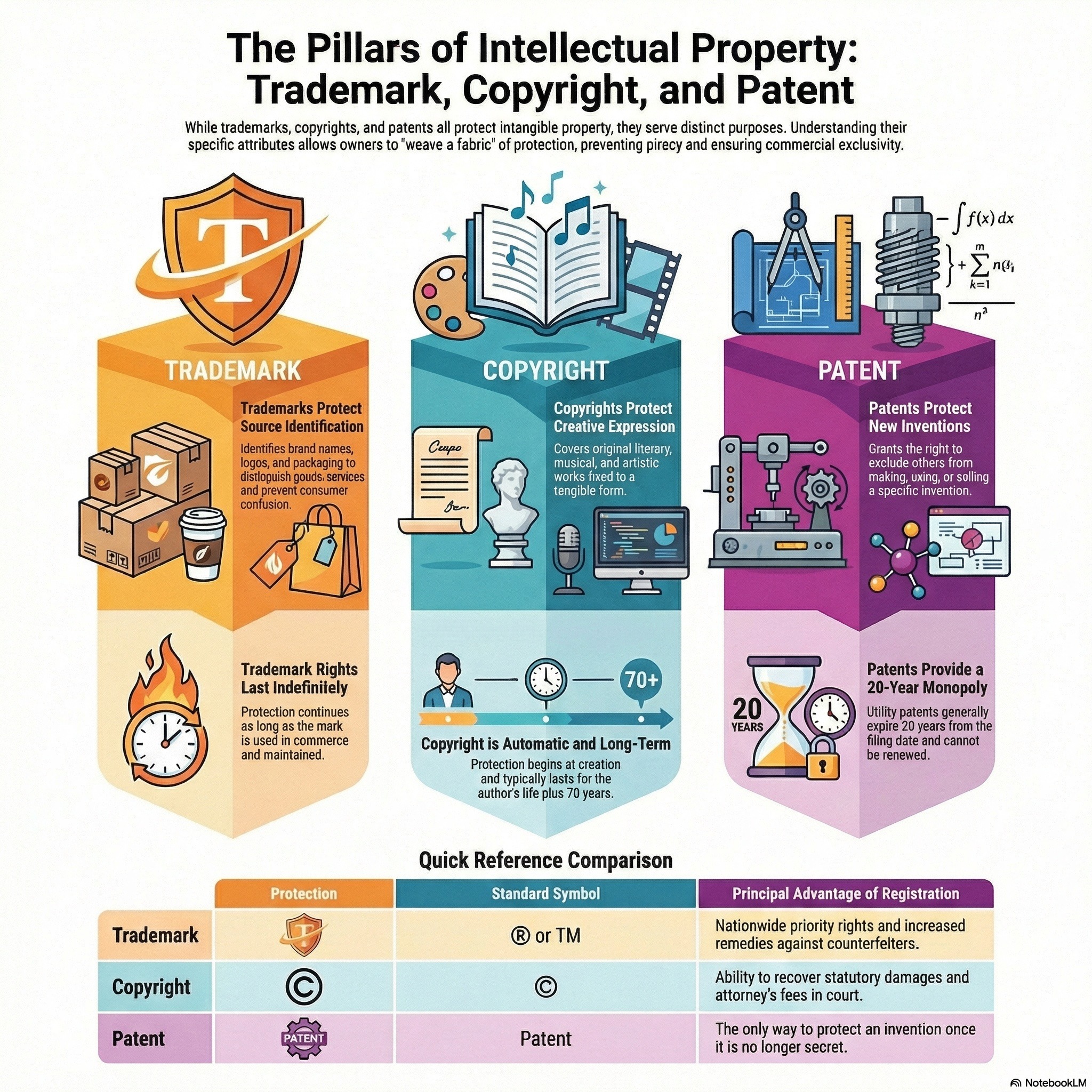
This podcast examines the complex legal and historical landscape of intellectual property, specifically focusing on copyrights, trademarks, and patents. One article outlines the evolution of the fair use defense in the software industry, while another explores how international systems distinguish between the flexible fair use approach and the rigid fair dealing rules. The United States Patent and Trademark Office provides practical guidance on the registration process and the necessity of avoiding consumer confusion. A biographical account of actress Hedy Lamarr highlights the real-world impact of patents, detailing her contribution to frequency-hopping technology. Finally, a satirical cartoon critiques the entertainment...
CVSS, CVE, VPR, & NVD
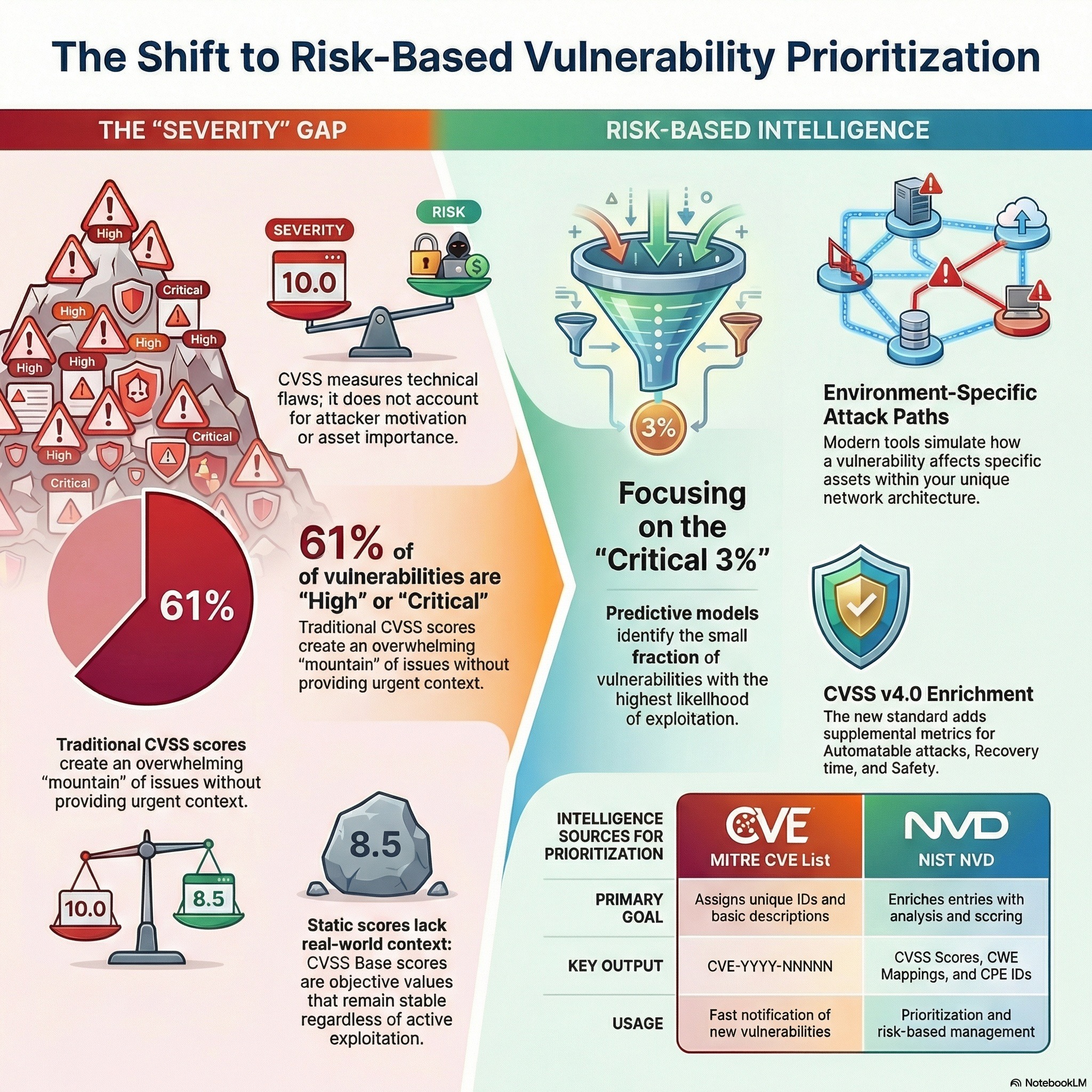
This podcast examines the essential frameworks used to identify, analyze, and rank security threats, specifically focusing on the roles of MITRE and the National Vulnerability Database (NVD). While MITRE serves as the primary authority for assigning CVE identifiers, the NVD enriches this data with CVSS scores to help organizations gauge the technical severity of vulnerabilities. The documentation highlights that CVSS measures severity rather than total risk, prompting the development of more dynamic systems like Tenable’s Vulnerability Priority Rating (VPR) and CVSS v4.0. These newer models integrate threat intelligence, environmental context, and supplemental metrics such as exploit maturity and sa...
MITRE ATT&CK, Lockheed Cyber Kill Chain, & The Diamond Model Of Intrusion Analysis

This podcast analyzes and compares three primary frameworks used in modern cybersecurity: the Lockheed Martin Cyber Kill Chain, the MITRE ATT&CK Matrix, and the Diamond Model of Intrusion Analysis. The Cyber Kill Chain offers a linear perspective on the stages of an attack, while MITRE ATT&CK provides an extensive database of specific adversary behaviors and technical methods. In contrast, the Diamond Model focuses on the underlying relationships between an attacker, their capabilities, the infrastructure used, and the ultimate victim. Experts suggest that integrating these models allows organizations to move beyond simple alerts toward a more strategic understanding...
NIST Cybersecurity Framework (NIST CSF)
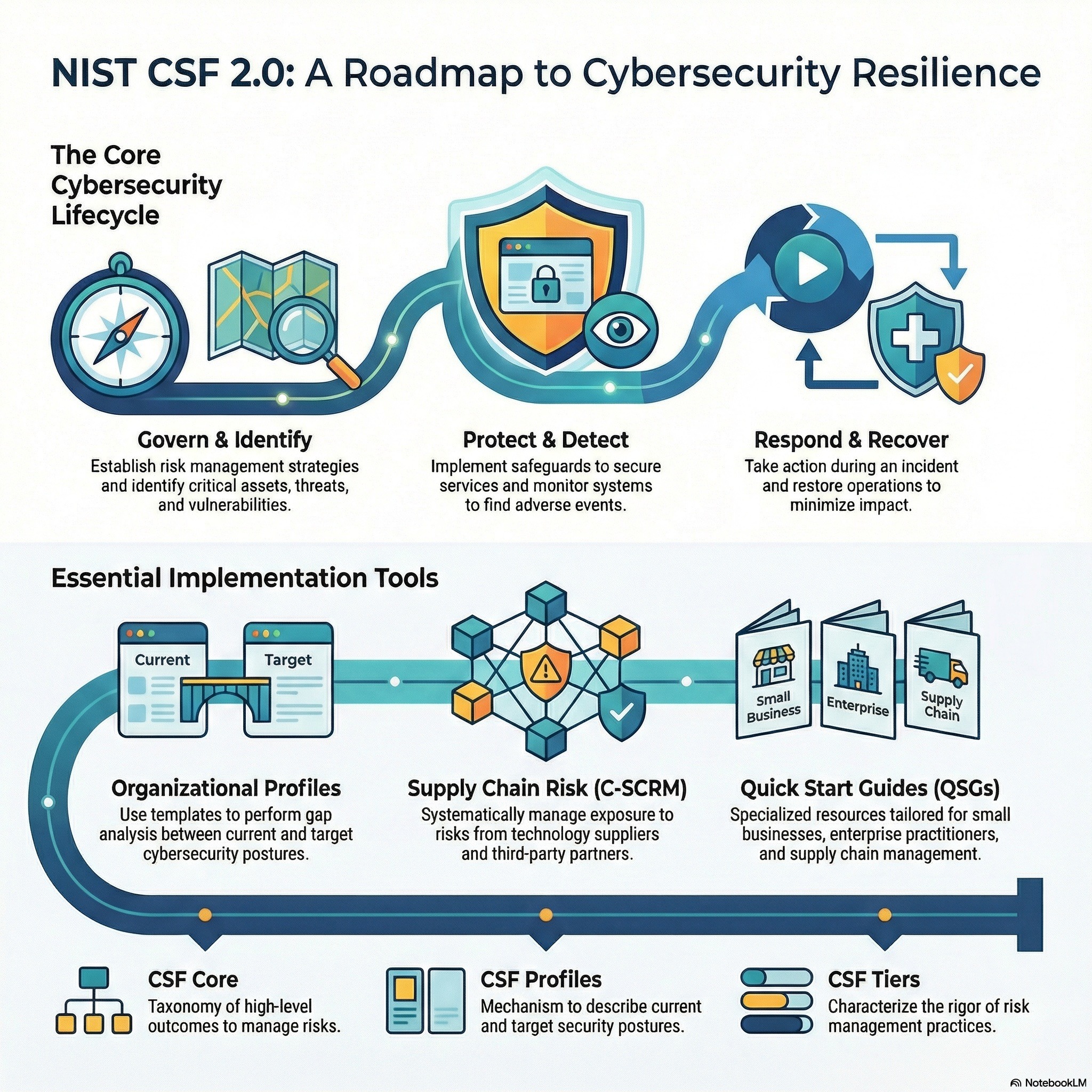
The NIST Cybersecurity Framework (CSF) 2.0 serves as a foundational guide for organizations of all sizes to manage and reduce cybersecurity risks through a standardized taxonomy of functions and outcomes. A central component of this manual is the use of Organizational Profiles, which allow entities to document their Current Profile of existing practices and define a Target Profile representing their desired security posture. By performing a Gap Analysis between these two states, organizations can identify deficiencies and build a prioritized Action Plan to improve their resilience. The framework is supported by a suite of online resources, including Implementation Examples for...
Security Analytics - Podcast 04 - Machine Learning Security Applications For Business
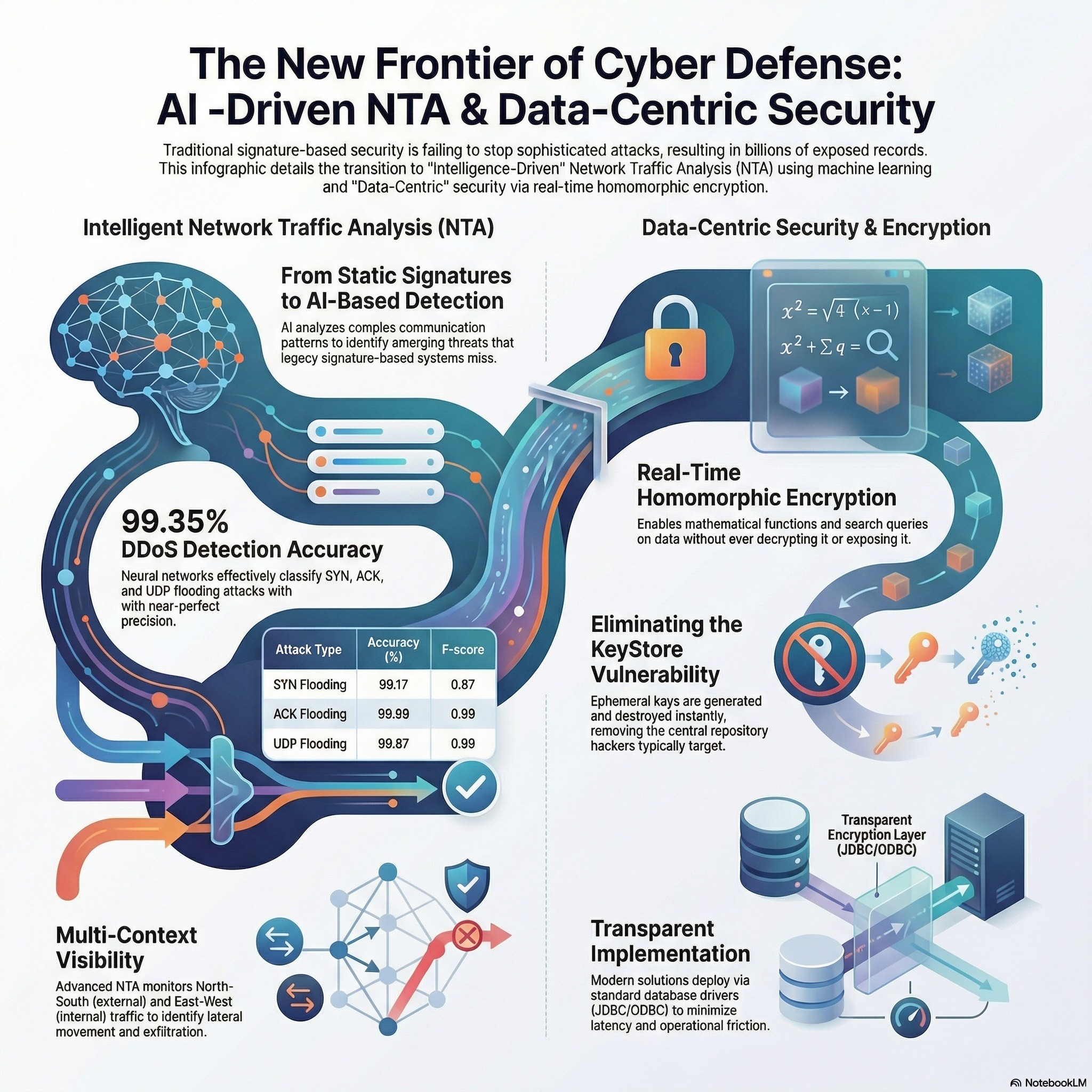
This podcast investigates advanced methods for enhancing cybersecurity through the application of machine learning. The primary study details the creation of a neural network specifically designed to identify and categorize DDoS flooding attacks, such as SYN and UDP flooding, with high precision. By utilizing a 24-106-5 architecture, the researchers achieved an accuracy rate of over 95% in both simulated and laboratory environments. A second source complements this by exploring the detection of pivoting activity, using statistical correlation and Principal Component Analysis to identify malicious movements within a network. Together, these sources demonstrate how automated data analysis can distinguish between...
AI RMF Podcast 09 - NIST AI 100 - 2e2025 - Adversarial Machine Learning
National Institute of Standards and Technology AI 100-2e2025, Adversarial Machine Learning, examines the security risks posed by malicious actors who intentionally manipulate machine learning systems and outlines strategies to strengthen their resilience. The report explains how adversarial attacks can occur during different phases of the AI lifecycle, including data poisoning during training, model evasion through carefully crafted inputs, model extraction, and inference-time manipulation. It emphasizes that AI systems introduce new attack surfaces beyond traditional cybersecurity threats, requiring specialized risk assessment, testing, and monitoring approaches. The publication promotes secure-by-design principles, robust evaluation techniques, red-teaming, and continuous monitoring to detect...
AI RMF Podcast 08 - OECD Framework For Classifying AI Systems
Organization for Economic Co-operation and Development Framework for Classifying AI Systems provides a structured method for categorizing AI systems based on their context, capabilities, and potential impact. Rather than ranking systems as simply “high” or “low” risk, the framework analyzes AI across multiple dimensions, including the system’s purpose, the data it uses, its degree of autonomy, the human involvement in decision-making, and the severity and scale of potential outcomes. It emphasizes lifecycle thinking—from design and development to deployment and monitoring—while encouraging policymakers and organizations to consider how AI systems interact with social, legal, and economic environments. The framework...
AI RMF Podcast 07 - NIST AI 100-5 - A Plan For Global Engagement On AI Standards
National Institute of Standards and Technology AI 100-5, A Plan for Global Engagement on AI Standards, outlines a strategic approach for advancing international collaboration in the development of AI standards. The publication emphasizes the importance of aligning technical standards, risk management practices, and governance frameworks across countries to promote innovation while safeguarding trust, safety, and human rights. It identifies key priorities such as strengthening U.S. participation in international standards bodies, fostering public–private partnerships, promoting interoperability, and supporting capacity-building efforts worldwide. The report underscores that AI is inherently global, requiring coordinated engagement to address shared challenges like bias, se...
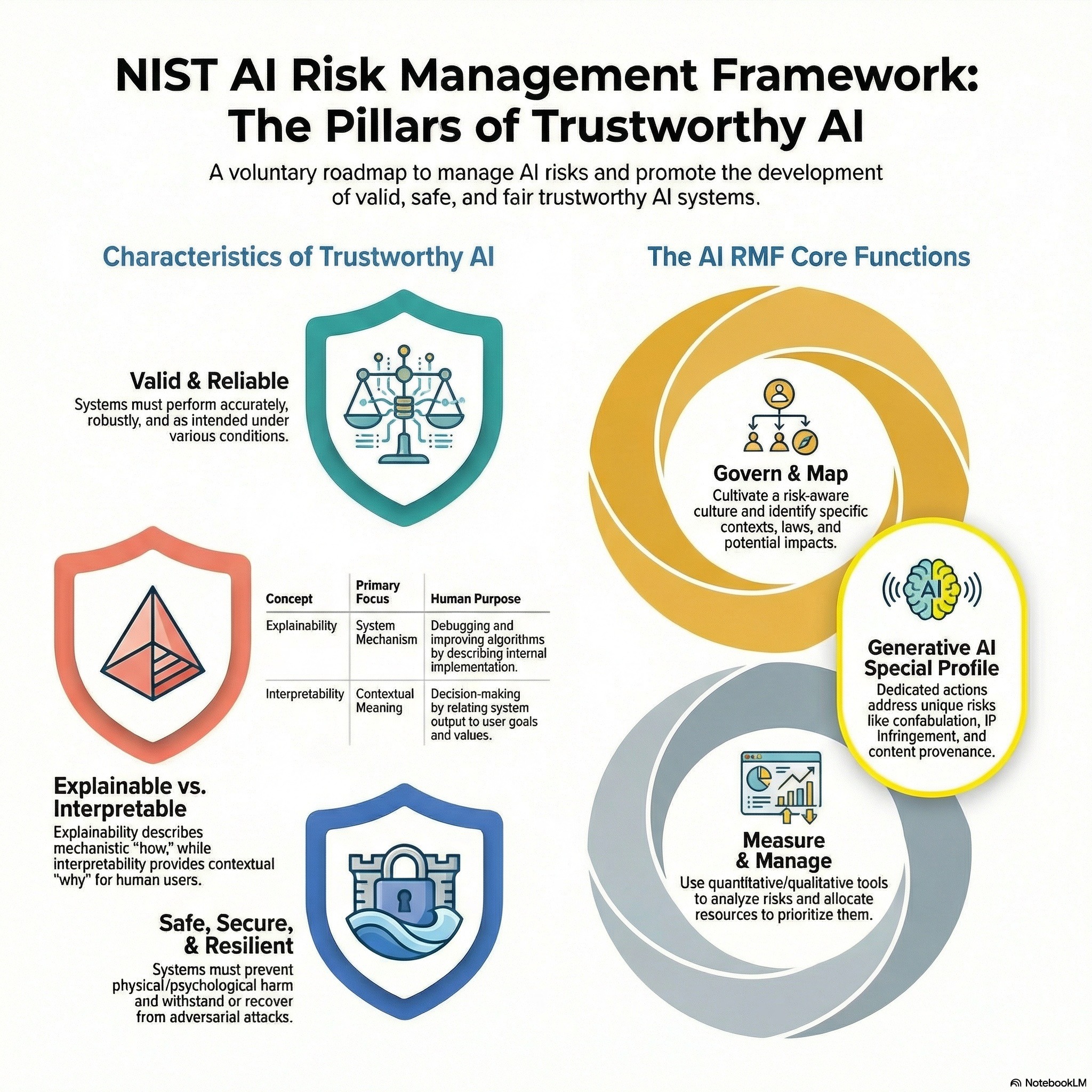
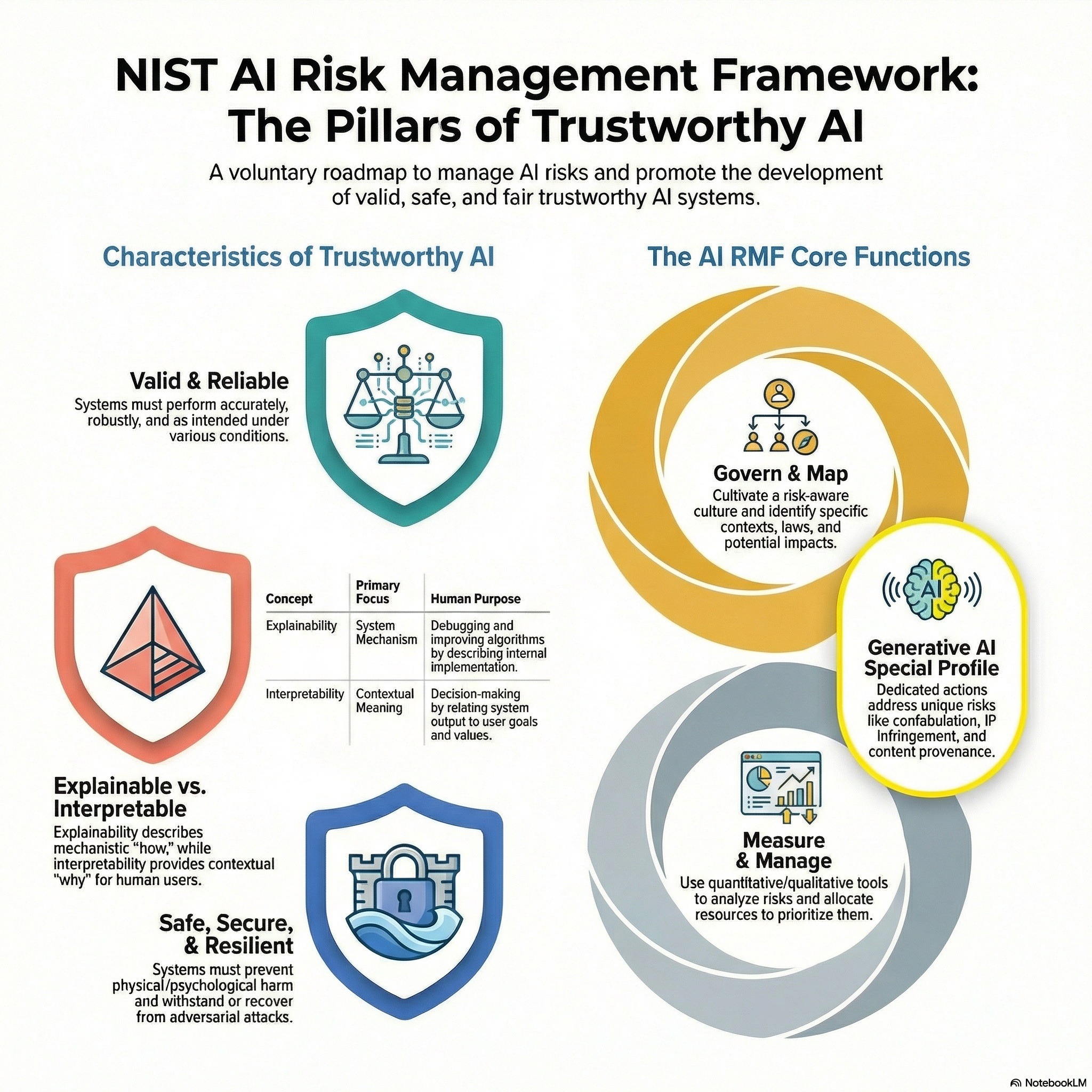
AI RMF Podcast 06 - NIST AI 100-3 - The Language of Trustworthy AI
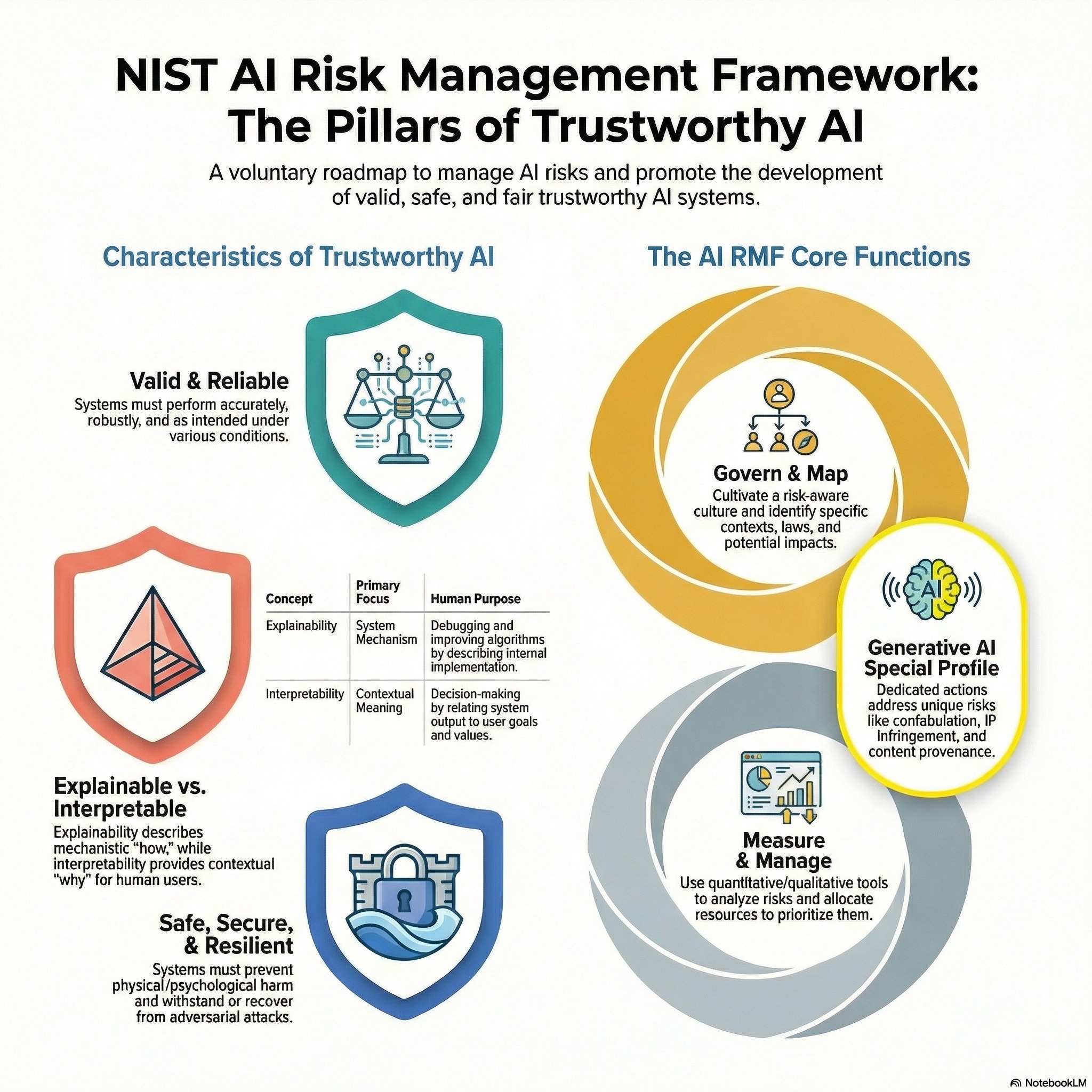
National Institute of Standards and Technology AI 100-3, The Language of Trustworthy AI, establishes a shared vocabulary to support consistent understanding and implementation of trustworthy artificial intelligence. The publication clarifies key concepts such as reliability, robustness, safety, security, resilience, privacy, fairness, accountability, transparency, and explainability, emphasizing that these characteristics are interconnected and context-dependent. By standardizing terminology, the report helps organizations, policymakers, and researchers communicate more precisely about AI risks, controls, and governance practices. It supports the broader AI Risk Management Framework by reducing ambiguity in how trustworthiness is defined and operationalized across sectors. Ultimately, NIST AI 100-3 promotes clearer...
AI RMF Podcast 05 - NISTIR 8367 - Psychological Foundations Of Explainability & Interpretability In AI
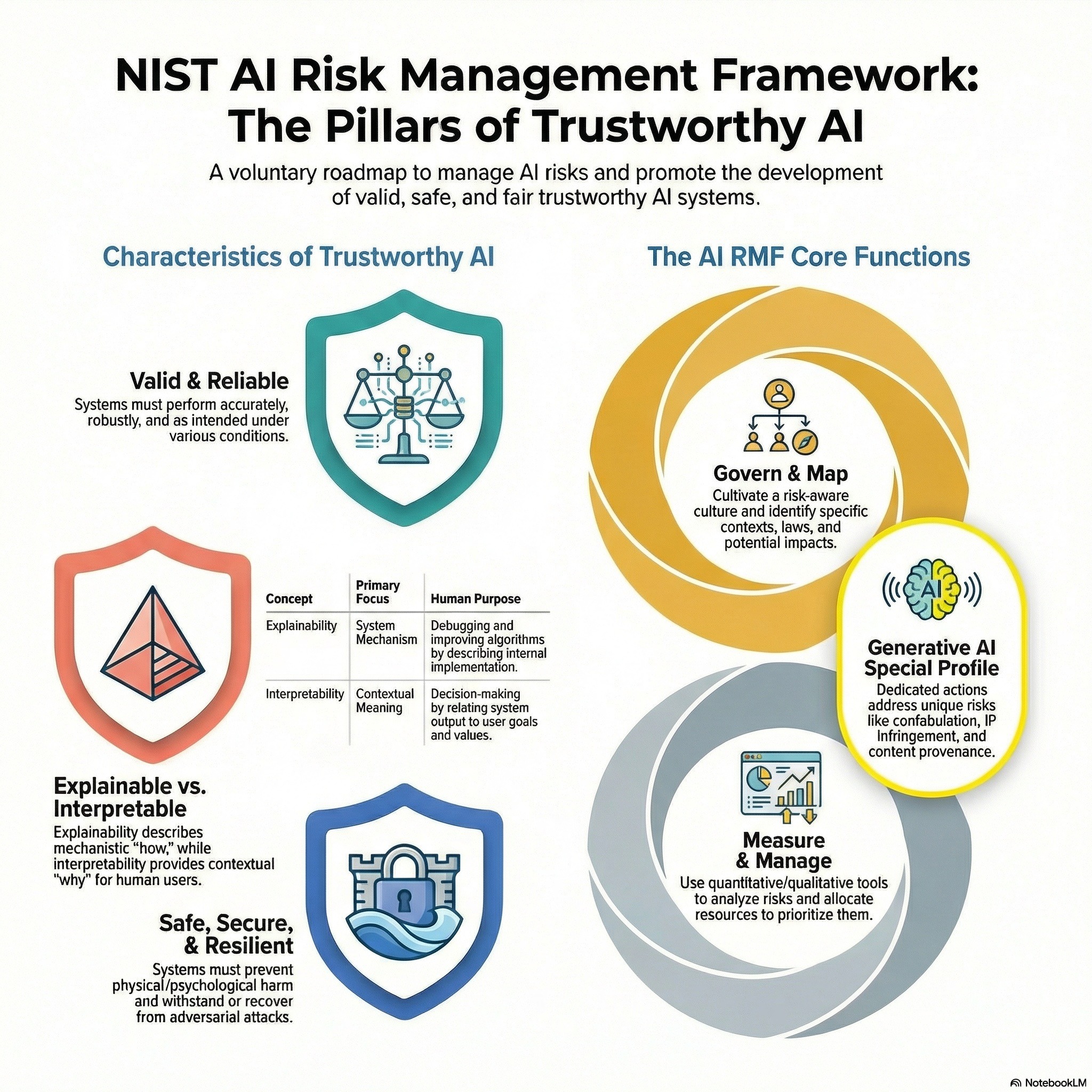
National Institute of Standards and Technology Interagency Report 8367, Psychological Foundations of Explainability and Interpretability in AI, examines explainable AI through the lens of human cognition and decision-making. Rather than focusing solely on technical transparency, the report emphasizes how people understand, trust, and interact with AI systems. It explains that effective explanations must align with human mental models, account for cognitive limitations, and support users’ goals, context, and expertise levels. The publication distinguishes between interpretability (how well a system’s internal mechanics can be understood) and explainability (how well a system communicates its reasoning to humans), highlighting that explanations must be a...
AI RMF Podcast 04 - NISTIR 8312 - Four Principles Of Explainable Artificial Intelligence
National Institute of Standards and Technology Interagency Report 8312, Four Principles of Explainable Artificial Intelligence, defines foundational guidance for designing AI systems that can be understood and trusted by users. The report outlines four core principles: AI systems should provide explanations for their outputs; those explanations should be meaningful and understandable to the intended audience; the explanations should accurately reflect how the system produced its results; and the system should operate only within the conditions for which it was designed and validated (knowledge limits). NISTIR 8312 emphasizes that explainability is context-dependent—what counts as a sufficient explanation varies across domains such as...
AI RMF Podcast 03 - NIST Special Publication 1270 - Towards A Standard for Identifying & Managing Bias In AI
This podcast outlines a structured approach to recognizing, measuring, and mitigating bias in artificial intelligence systems. The NIST publication distinguishes between statistical bias (systematic error in model outputs) and societal bias (inequities embedded in data and social systems), emphasizing that AI systems can both reflect and amplify existing disparities. It proposes a lifecycle-based framework that spans data collection, model development, evaluation, deployment, and monitoring, encouraging organizations to adopt transparency, documentation, testing, and stakeholder engagement practices. The report highlights the importance of clear definitions, contextual understanding of fairness, and measurable performance criteria, while acknowledging trade-offs among fairness metrics. Ultimately, SP 1270...
AI RMF Podcast 02 - NIST Generative AI Risk Management (AI 600-1 )
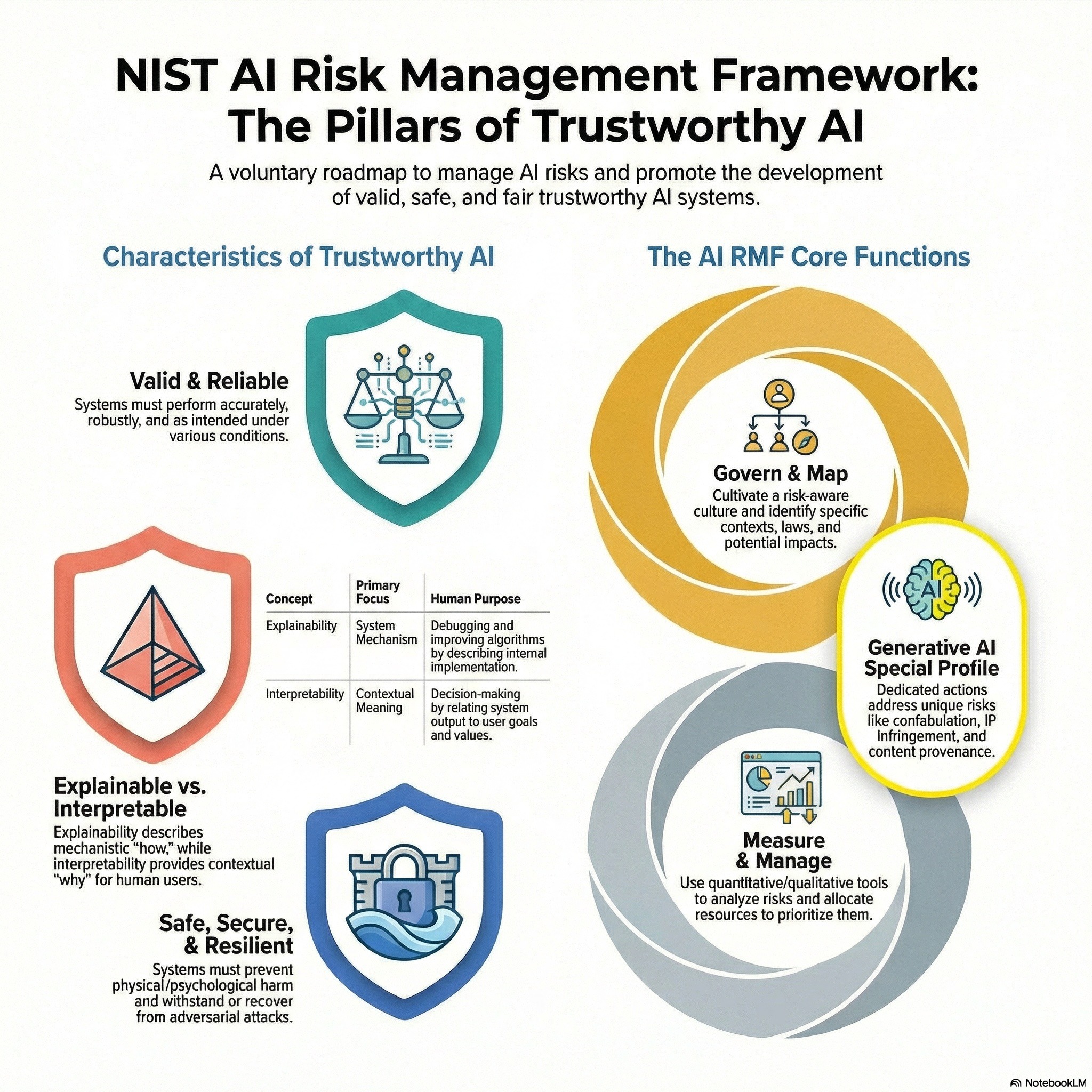
This podcast explores the core elements of NIST AI 600-1, a framework designed to help organizations identify, measure, and manage the unique and often amplified risks associated with generative AI systems. It highlights twelve central risk areas, including confabulation, dangerous or violent content, data privacy concerns, environmental impact, harmful and systemic bias, human–AI configuration challenges, information security threats, intellectual property risks, obscene or abusive outputs, and vulnerabilities across the AI value chain. The discussion also focuses on practical, cross-sector, and voluntary actions organizations can take to govern, map, measure, and manage these risks effectively. Special emphasis is placed on...
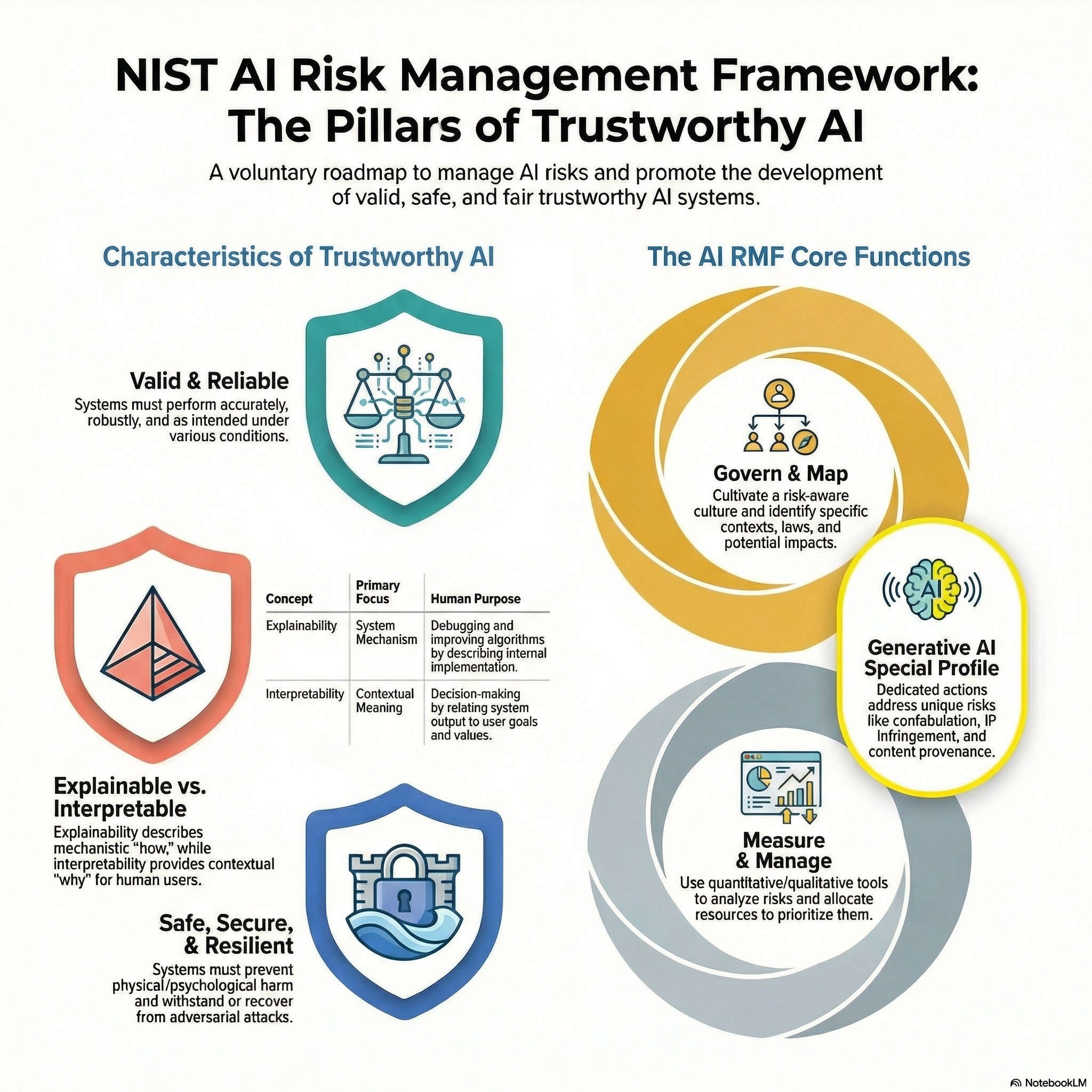
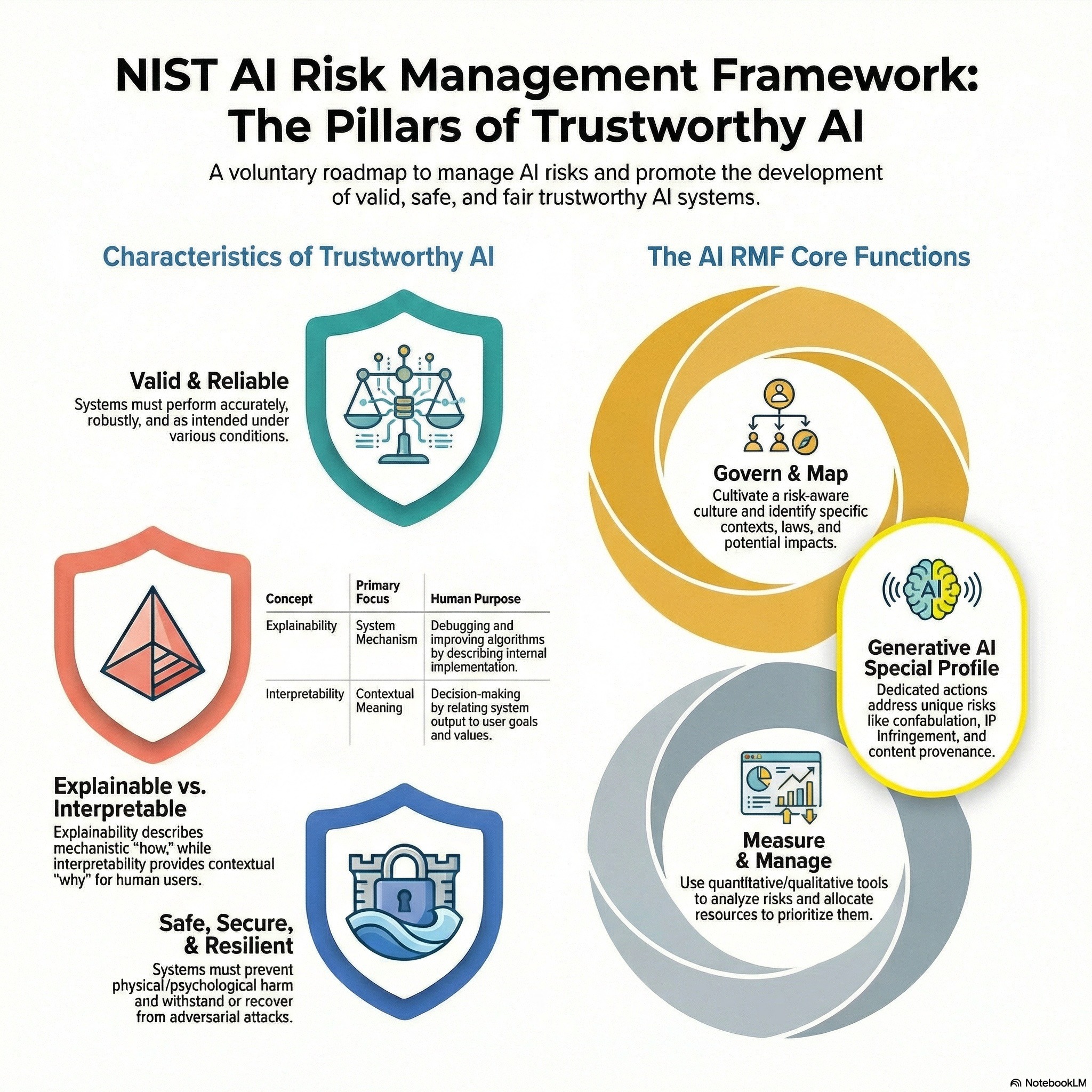
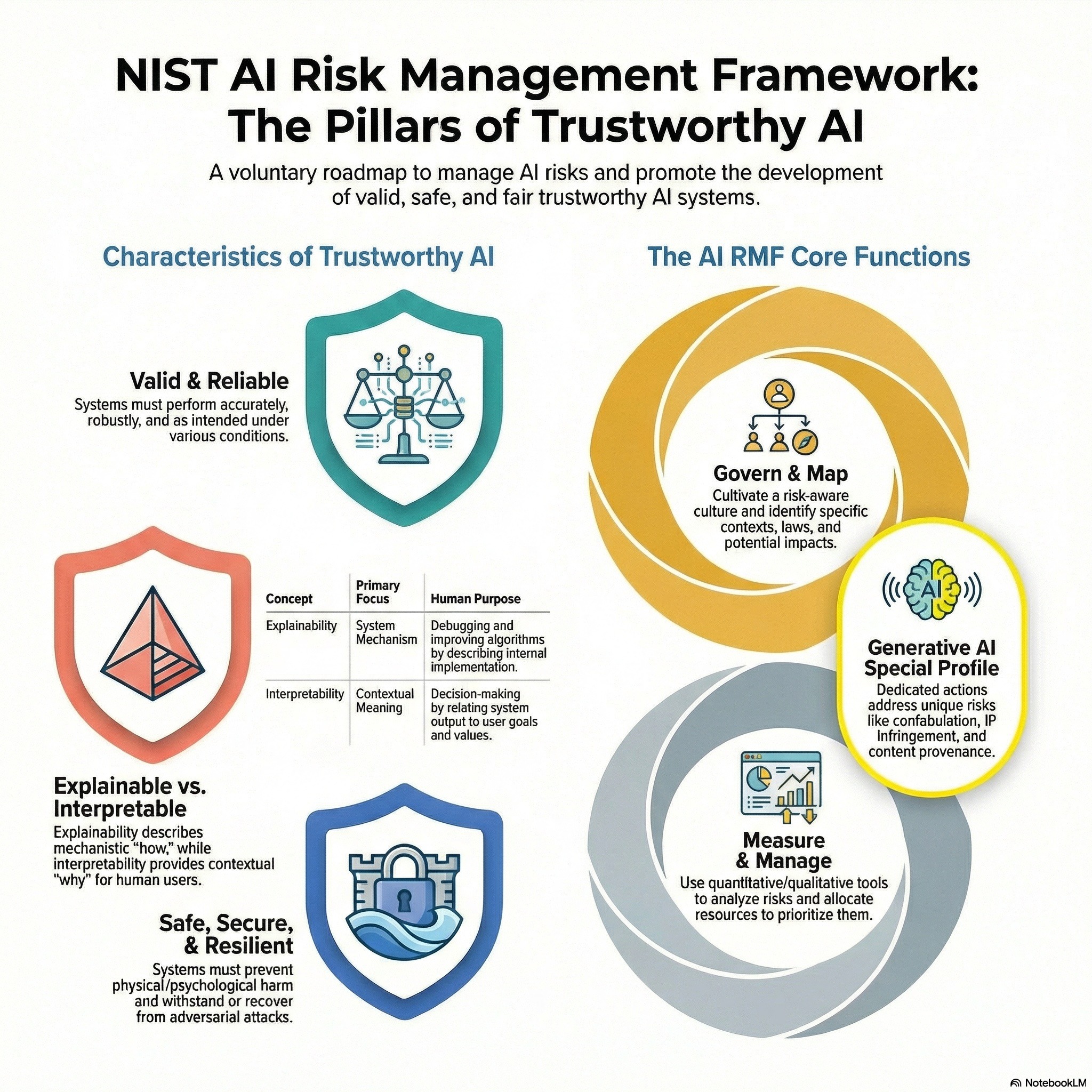
AI RMF Podcast 01 - NIST Artificial Intelligence Risk Management Framework
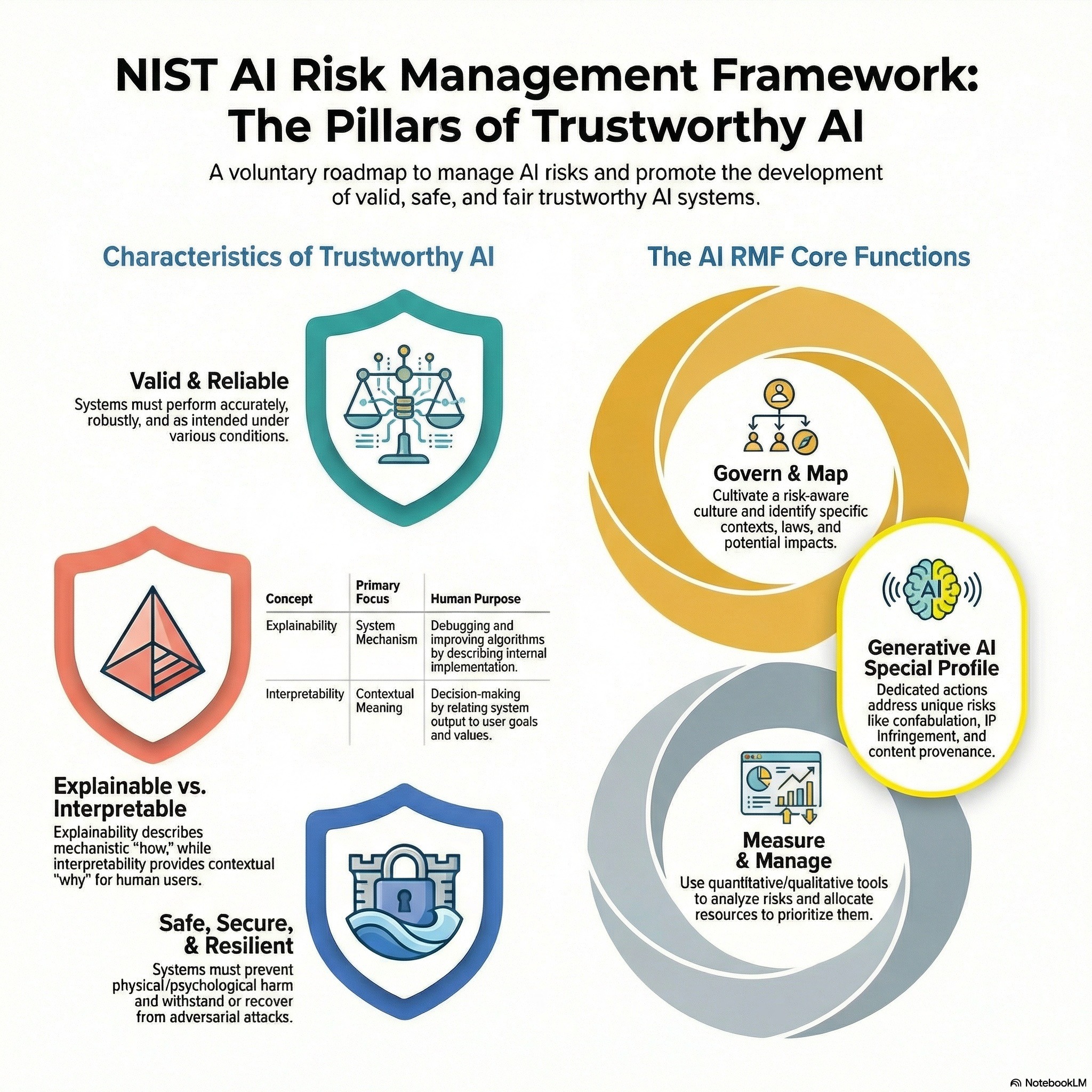
This podcast centers on the NIST AI Risk Management Framework (AI RMF), a voluntary standard designed to increase the trustworthiness of artificial intelligence through four key functions: govern, map, measure, and manage. While the core NIST documents establish foundational principles for mitigating sociotechnical harms—including specific risks like confabulation and bias in generative AI—supplementary research introduces a maturity model to help organizations operationalize these guidelines. This model provides a structured questionnaire and scoring system based on metrics such as robustness, coverage, and stakeholder diversity. By bridging the gap between high-level ethics and day-to-day practices, these resources offer a road...
CGRC - Domain 7 - Continuous Monitoring & Ongoing Authorization
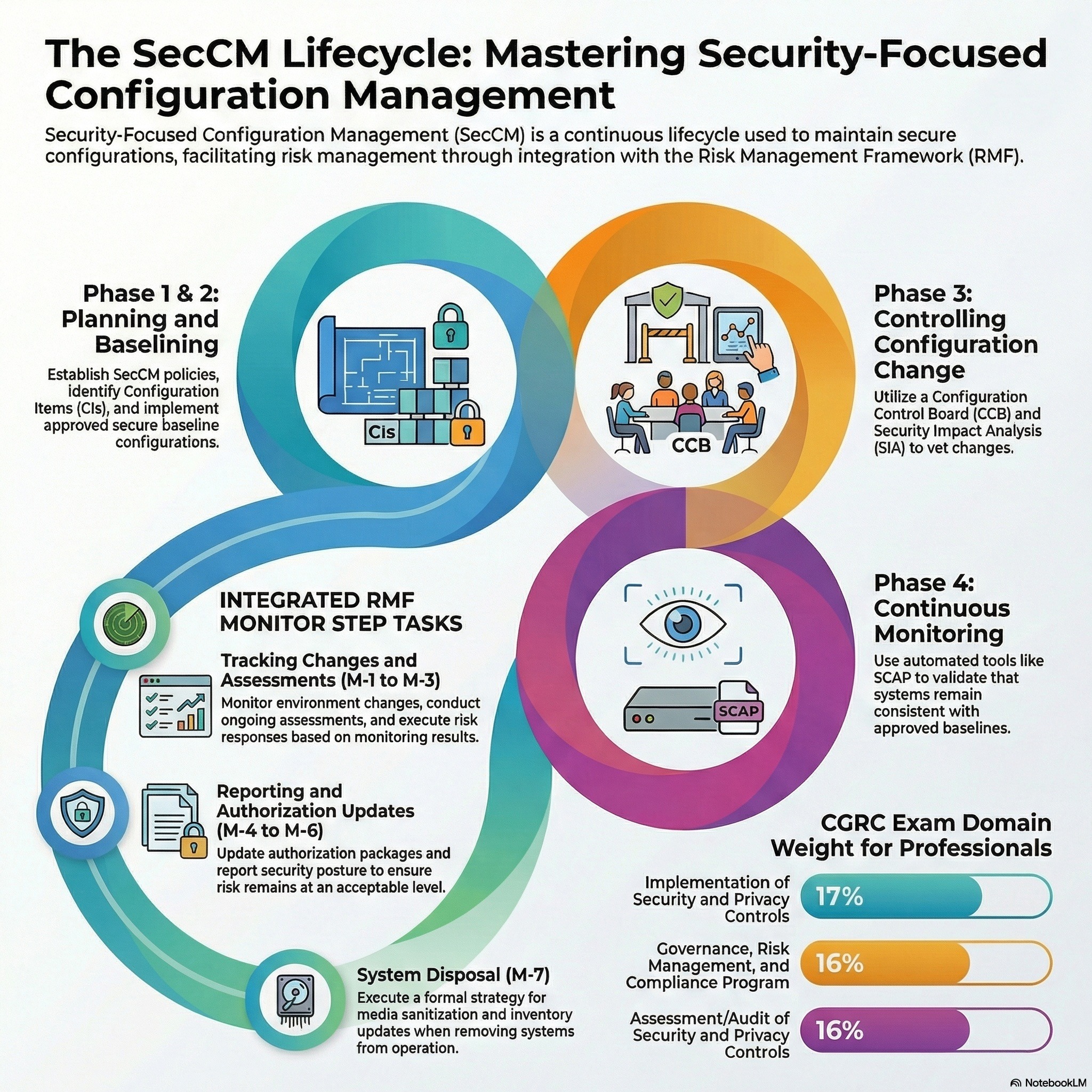
This podcast outlines the continuous monitoring phase of the Risk Management Framework (RMF), emphasizing the need for ongoing situational awareness in federal information systems. The provided text details how organizations must systematically track changes to technology, personnel, and operational environments to ensure that security and privacy controls remain effective over time. Key processes include performing security impact analyses, conducting regular audits, and utilizing automated tools like SCAP and SIEM for efficient data collection. The documentation also highlights the importance of reporting risk posture to authorizing officials to support near real-time authorization decisions. Finally, the guides address the end of...
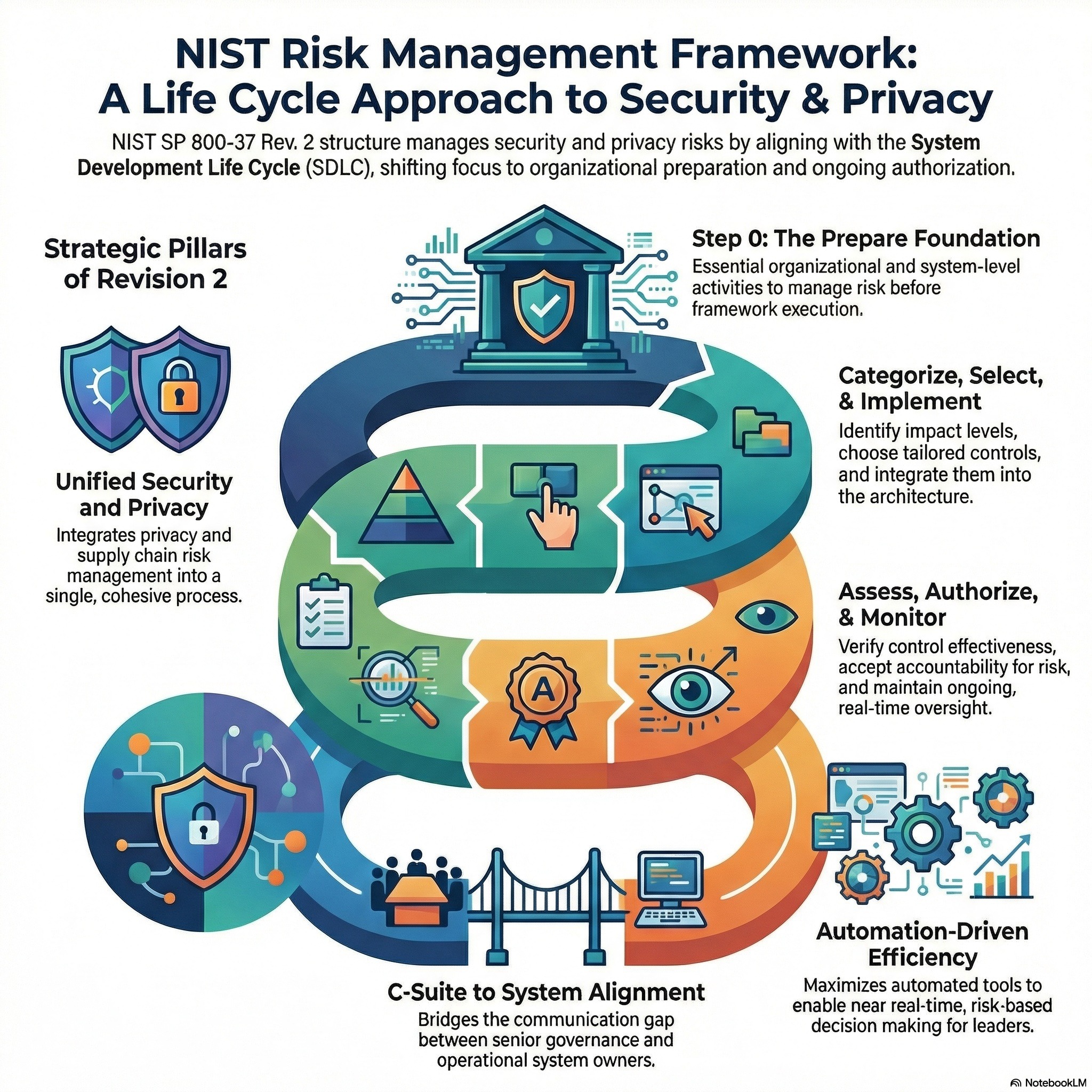
CGRC - Domain 6 - Risk Acceptance Demands Budget Authority
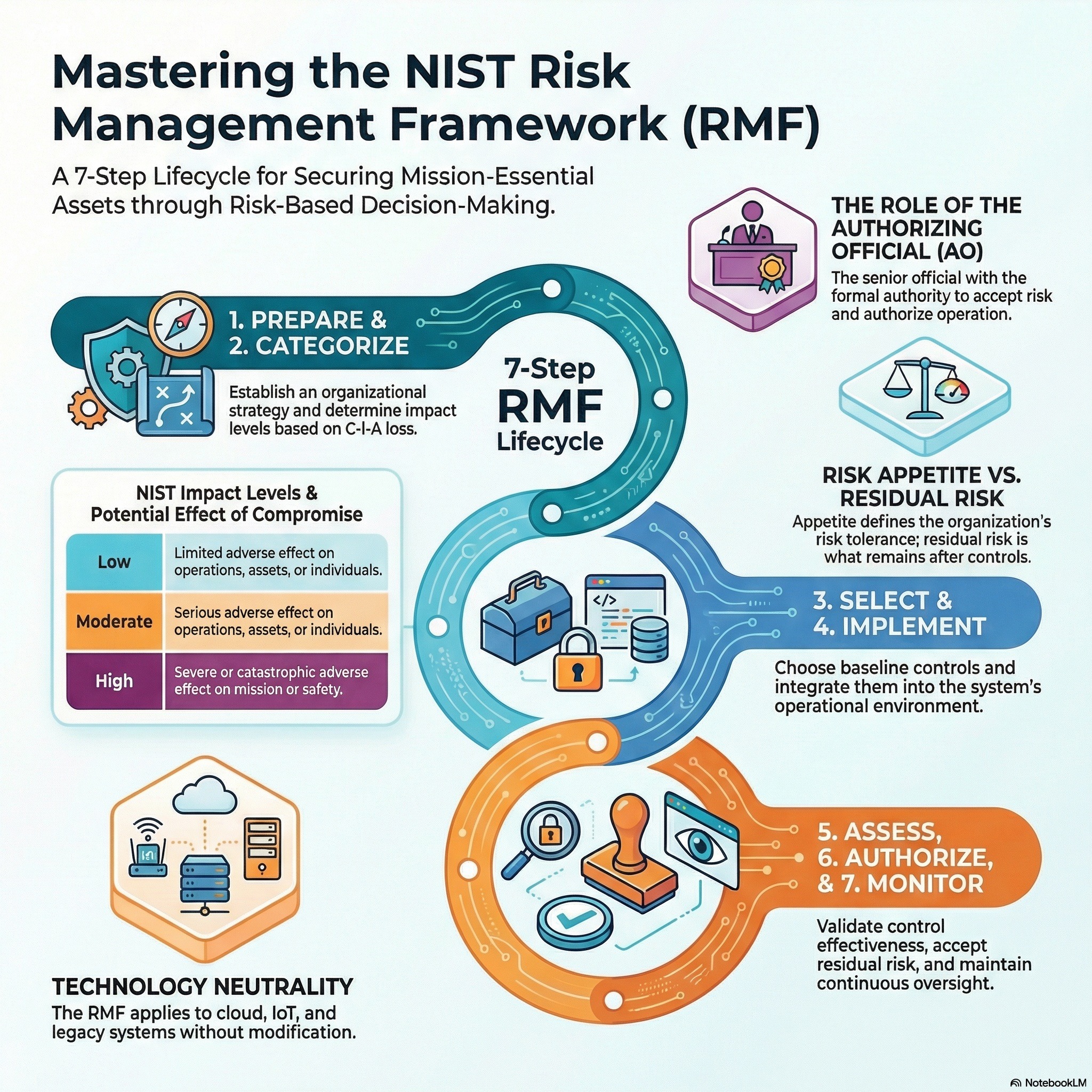
This podcast outlines essential strategies for professionals to manage technology and organizational risk through certifications and structured frameworks. One source highlights specific credentials for mastering vibe coding, CI/CD, and Agentic AI to prove technical proficiency to employers. The remaining sources detail the NIST Risk Management Framework (RMF), a comprehensive seven-step process designed to integrate security and privacy into the system development life cycle. This framework emphasizes continuous monitoring, risk assessment, and the establishment of clear accountability for protecting federal information systems. By following these guidelines, organizations can make informed, cost-effective decisions regarding the authorization and operation of their...
CGRC - Domain 5 - Proving Security Controls With NIST 800-53A
The provided podcast outlines the Risk Management Framework (RMF) developed by NIST to help organizations secure information systems and manage privacy risks. These materials explain how to categorize systems, select and implement security controls, and perform rigorous assessments to ensure safeguards function correctly. Key publications like SP 800-37 and SP 800-53A establish a structured process for authorizing systems and maintaining an acceptable security posture through continuous monitoring. The sources also highlight the importance of integrating privacy protections and risk mitigation strategies early into the system development life cycle. Furthermore, practical guidance is offered on documenting compliance, assigning organizational...
CGRC - Domain 4 - Hardening Systems & Documenting RMF Controls
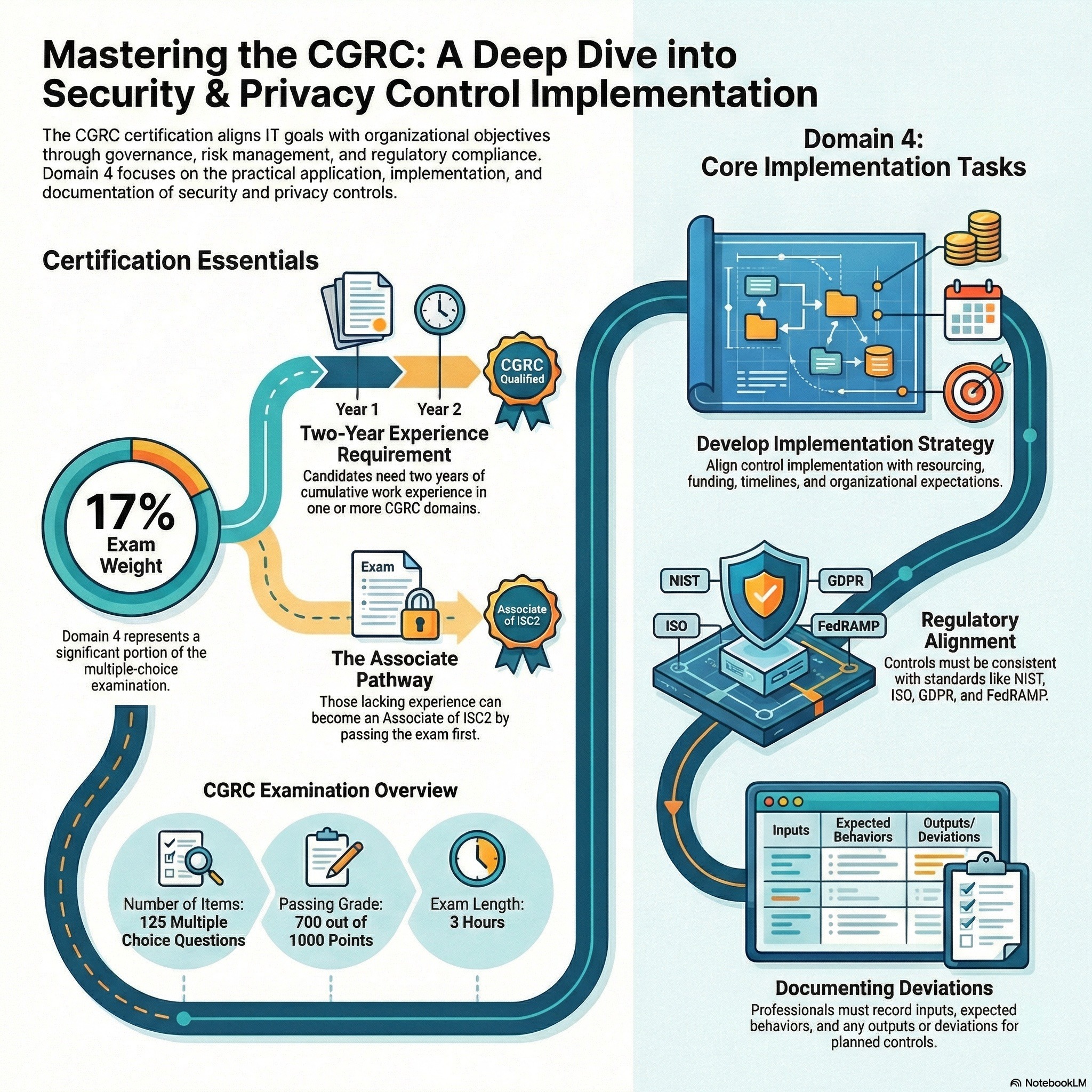
This podcast details the governance, selection, and application of security and privacy controls within the NIST Risk Management Framework. The documentation outlines the CGRC certification requirements, emphasizing continuous compliance, asset monitoring, and stakeholder communication throughout a system's life cycle. Central to these sources is the NIST SP 800-53 catalog, which provides a comprehensive set of safeguards ranging from access enforcement to incident response protocols. Practical guidance is included on tailoring control baselines to meet specific organizational missions and impact levels. Furthermore, the texts describe the necessity of remediation plans, formal assessments, and technical enhancements to mitigate risks from advanced...
CGRC - Domain 3 - Selecting and Tailoring NIST Security Control
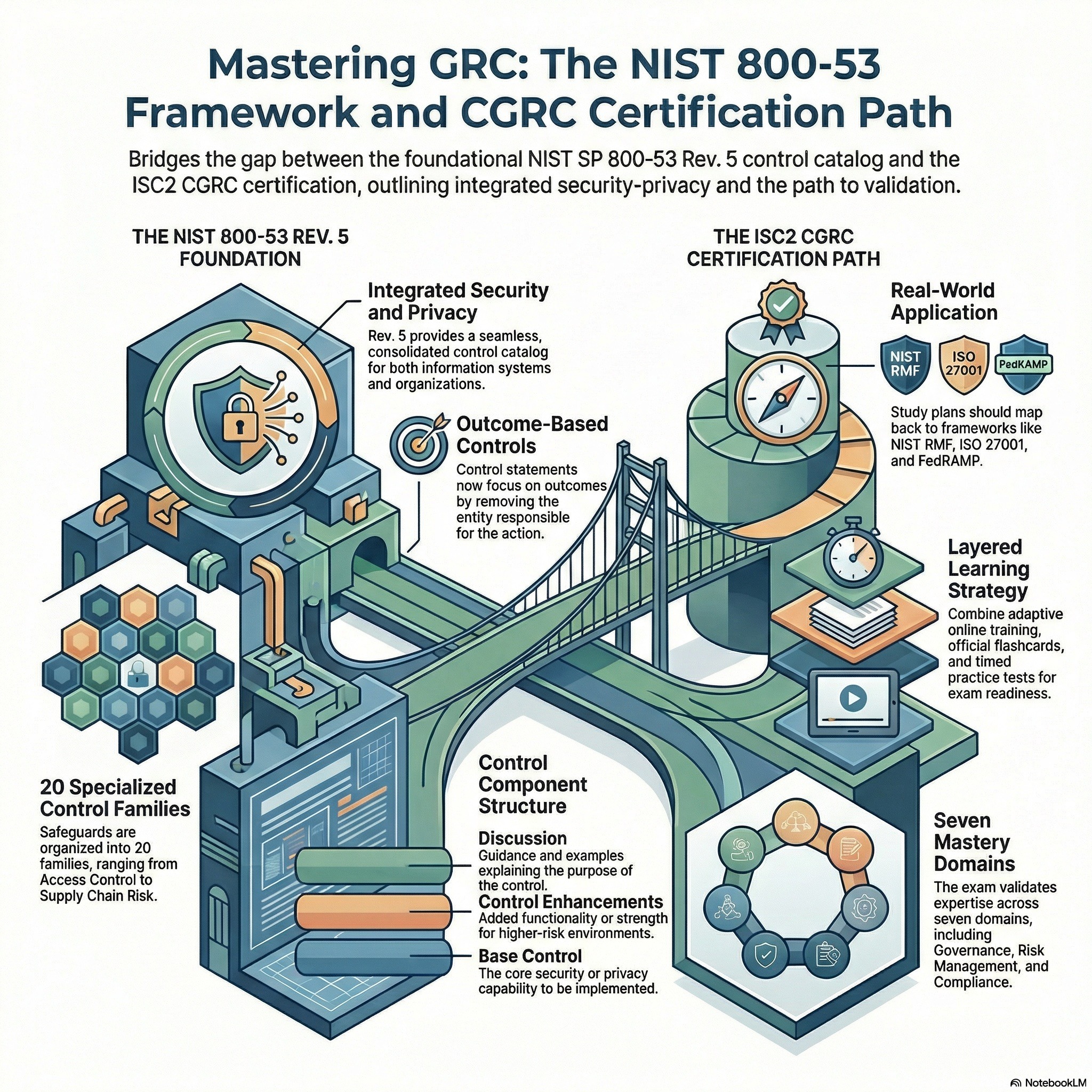
These sources detail the essential frameworks and training resources used to maintain robust cybersecurity and privacy standards within modern organizations. One document serves as a comprehensive catalog of technical controls, such as NIST SP 800-53, which outlines specific requirements for access management, incident response, and system integrity. Complementing these technical guidelines, the other source highlights professional certification and exam preparation programs for various IT and security roles. Together, they emphasize the importance of systematic risk management through both automated technical safeguards and the formal education of personnel. By integrating these protocols, entities can better protect personally identifiable information and...
CGRC - Domain 2 - Mastering CGRC Domain 2 Scope & Categorization
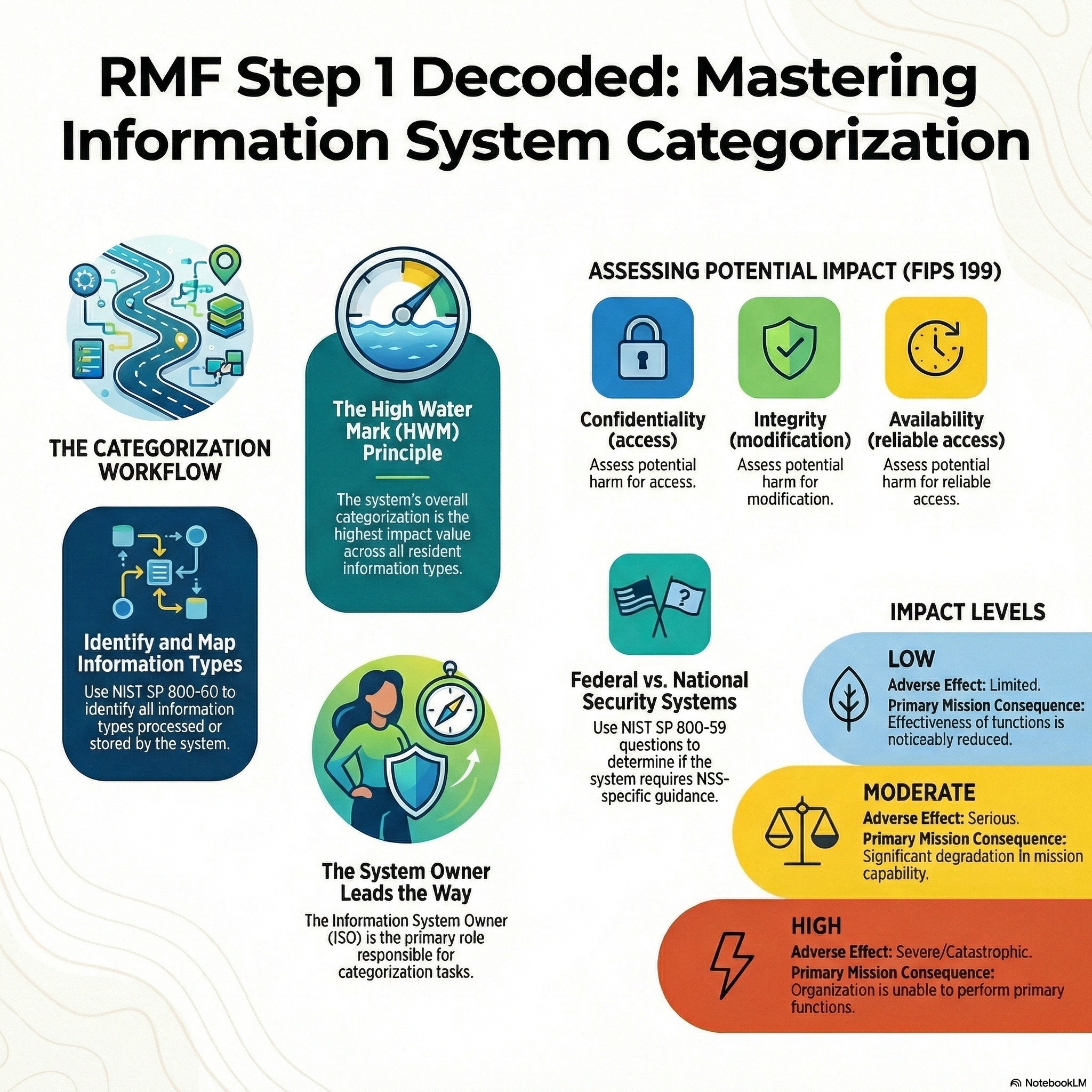
These materials collectively outline the Risk Management Framework (RMF) and its critical role in securing federal information systems. The documentation, which includes ISC2 training guides and NIST special publications, focuses heavily on the initial stages of the RMF, specifically the categorization of information systems based on security objectives like confidentiality, integrity, and availability. Detailed guidance is provided on establishing authorization boundaries, developing system security plans, and assigning impact levels to various information types. The sources also emphasize the importance of the System Development Life Cycle (SDLC) and the collaboration required between officials to manage organizational risk. Additionally, community discussions...
CGRC - Domain 1 - Mastering CGRC Domain 1 Governance and Risk
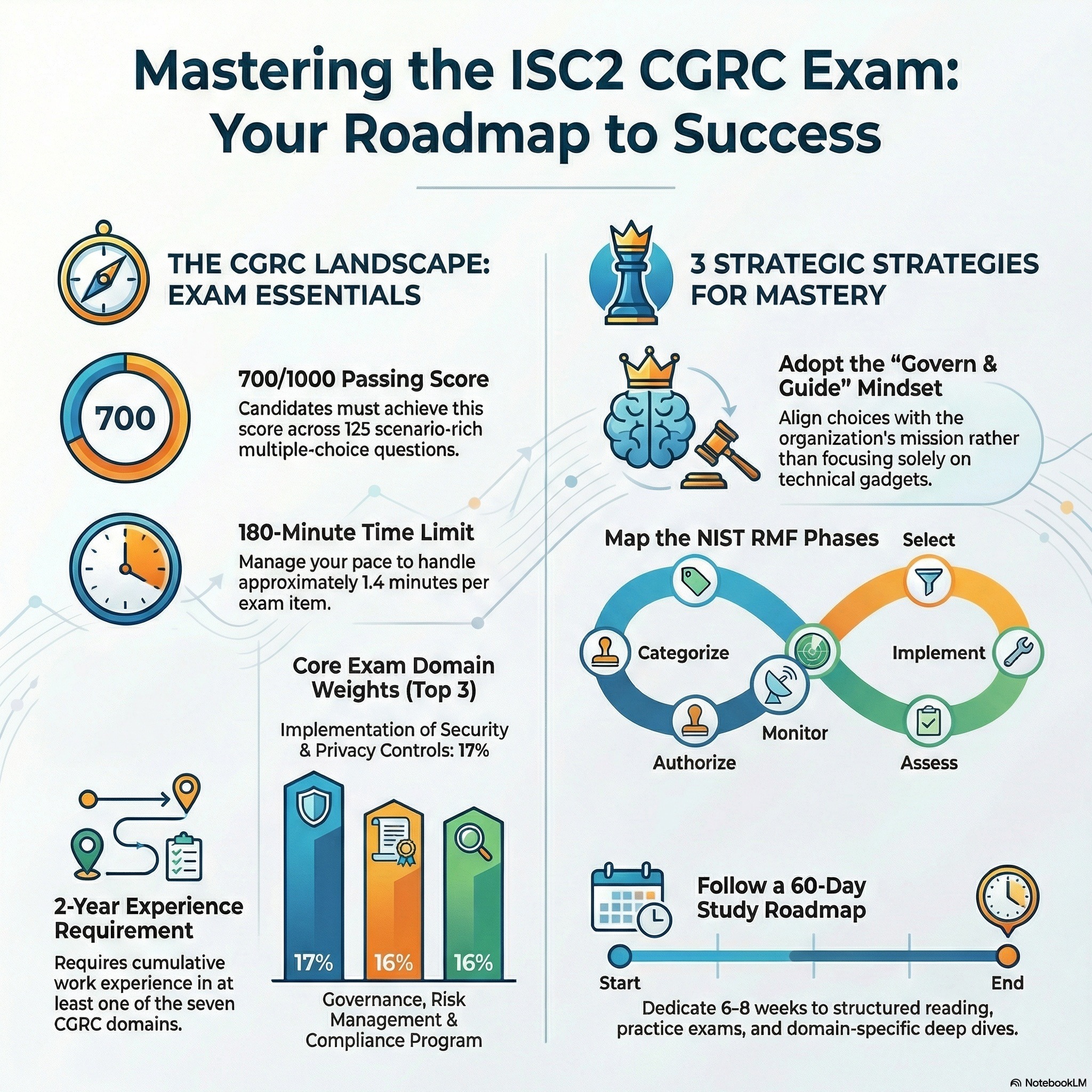
This instructor guide provides a foundational look at the Risk Management Framework (RMF) and the federal mandates that govern it. The material focuses on essential legislation like FISMA and the Privacy Act, while outlining how NIST standards and OMB circulars direct the protection of strategic information. To help candidates understand practical execution, the text details various organizational roles, ranging from the Head of Agency to the Security Control Assessor. It also explores risk assessment methodologies, emphasizing the process of framing, responding to, and monitoring threats. Finally, the source uses real-world examples, such as flight simulators and healthcare systems, to...
CAP - Domain 1 - Understanding The Risk Management Framework
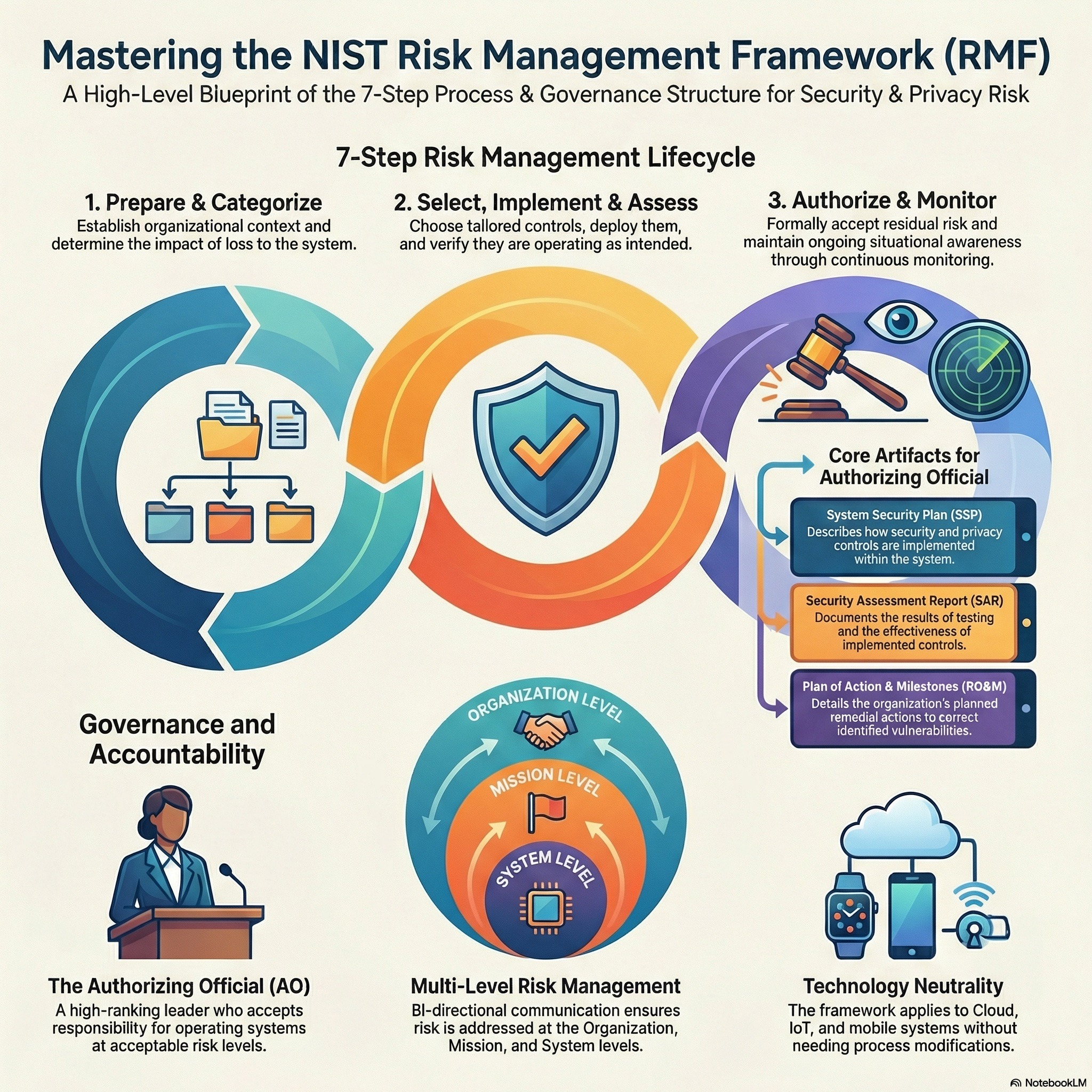
These sources establish a comprehensive regulatory and operational framework for managing information security risk within federal and national security environments. They detail essential legislation and mandates, such as FISMA and various OMB circulars, while providing standardized definitions for key concepts like risk, impact, and adequate security. Central to the material is a multi-tiered risk management approach that connects high-level organizational strategy to specific mission processes and individual information systems. The documentation outlines the specific roles and responsibilities of personnel, including Authorizing Officials and System Owners, across the six-step Risk Management Framework. Practical application is demonstrated through detailed case studies...
NIST Risk Management Framework (RMF)
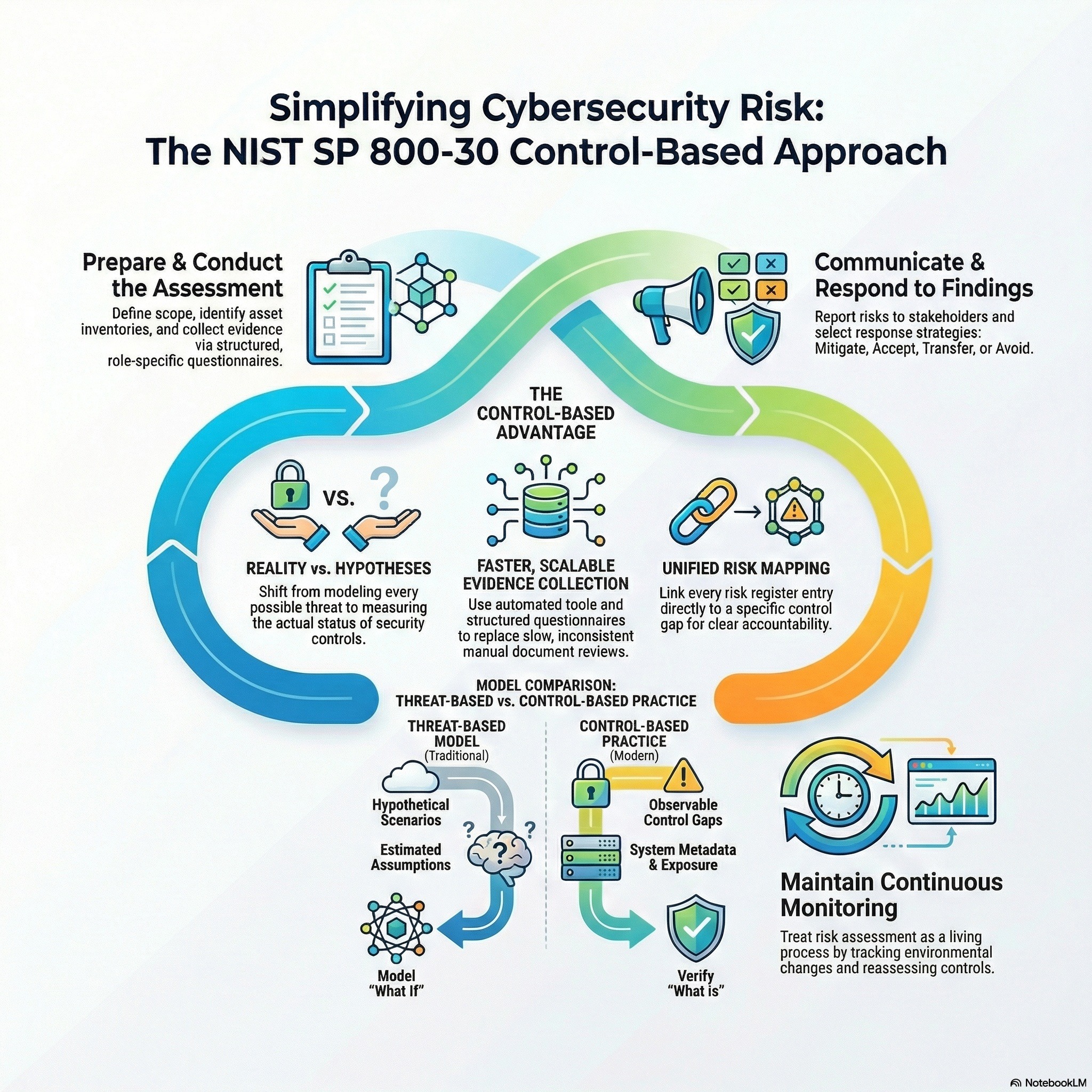
The provided documents outline the National Institute of Standards and Technology (NIST) guidelines for managing security and privacy risks within federal information systems and private organizations. Central to these sources is Special Publication 800-53, which provides an extensive catalog of security controls designed to protect the integrity, confidentiality, and availability of data. This framework encourages a collaborative risk management approach involving multiple government agencies to ensure that safeguards are both flexible and cost-effective. Furthermore, the texts explain how organizational risk tolerance dictates whether a threat should be mitigated or accepted based on mission priorities. Technical details regarding configuration management...
Ethics & Privacy - Podcast 05 - Mob Justice, Deepfakes, & Industrialized Crime
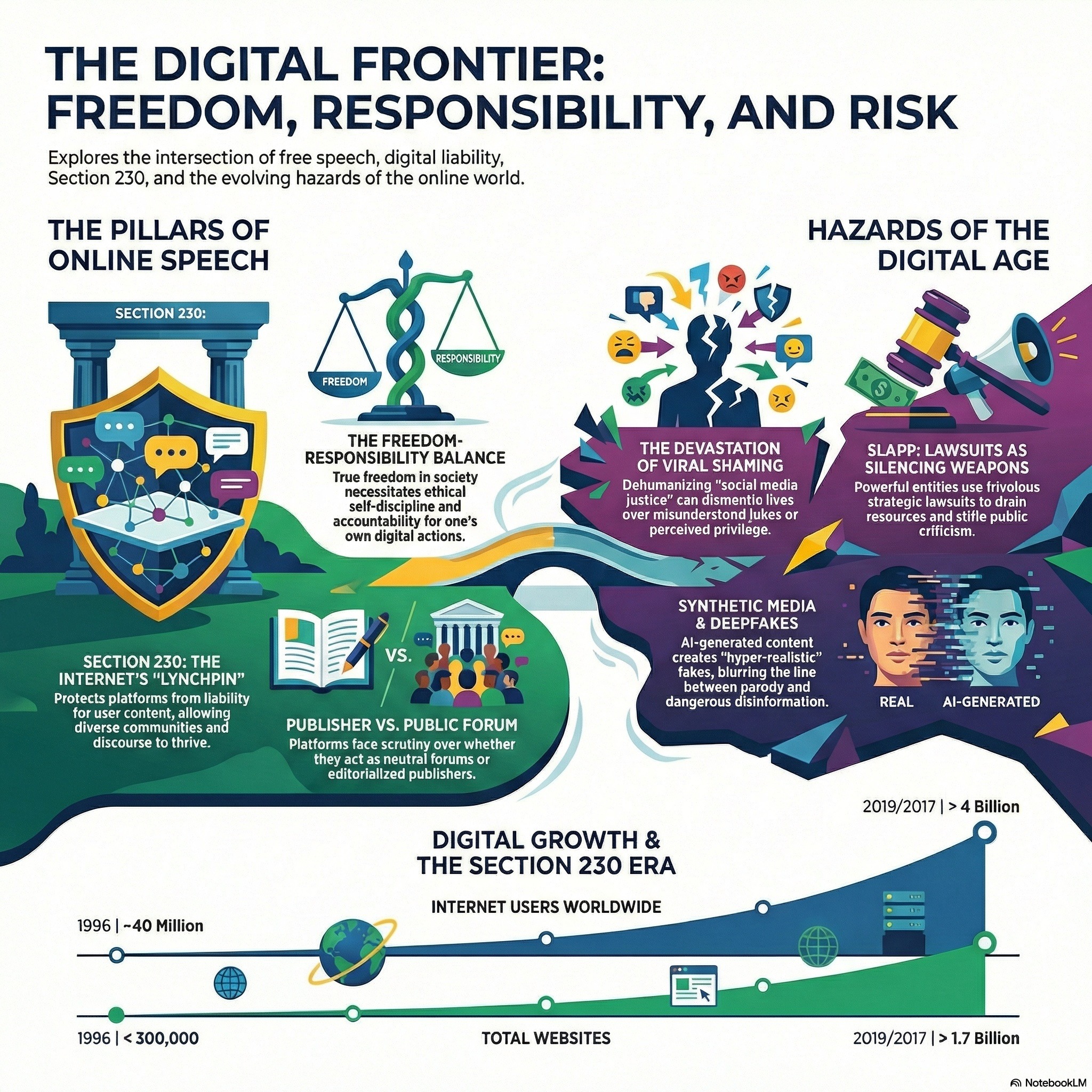
These sources examine the intricate relationship between individual freedom, technological disruption, and the legal frameworks that govern modern expression. One perspective focuses on the philosophical balance between personal liberty and the weight of moral responsibility, highlighting the importance of these values in maintaining a stable society. This theoretical foundation is challenged by the rise of synthetic media and deepfakes, which use artificial intelligence to create hyper-realistic but fraudulent content that threatens public trust. The materials further explore how powerful entities use SLAPP suits to silence criticism, turning the legal system into a tool for harassment and censorship. Ultimately, the...
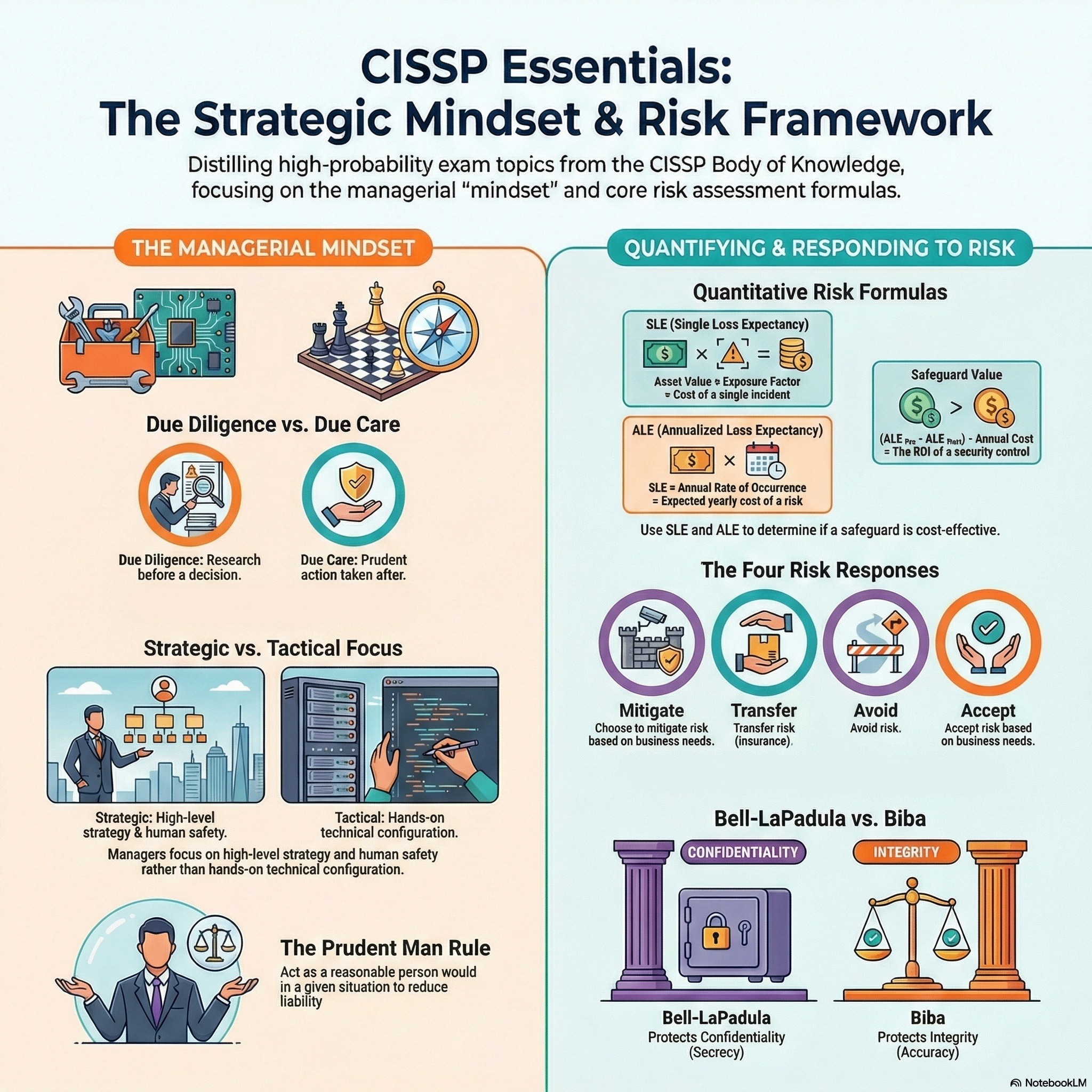
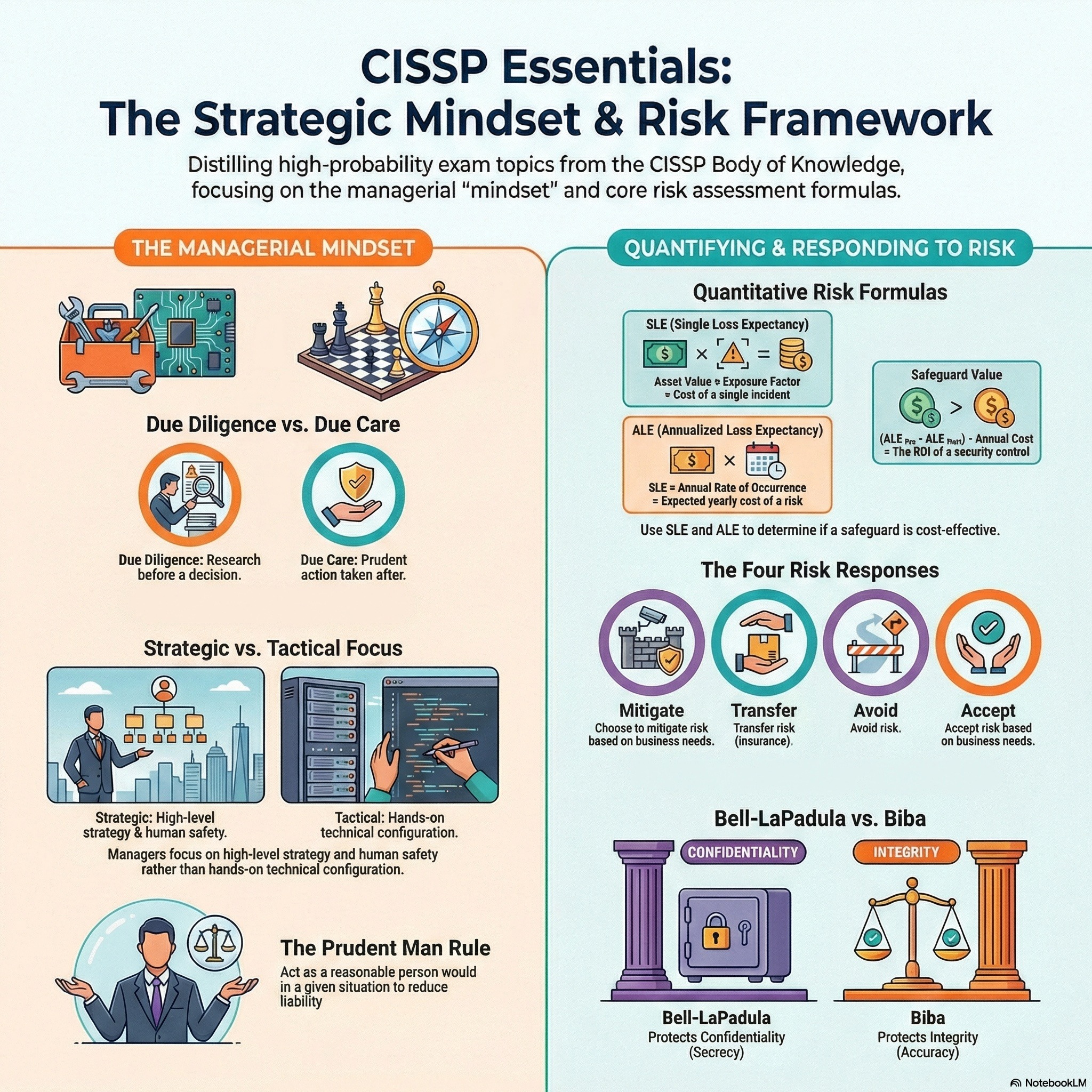
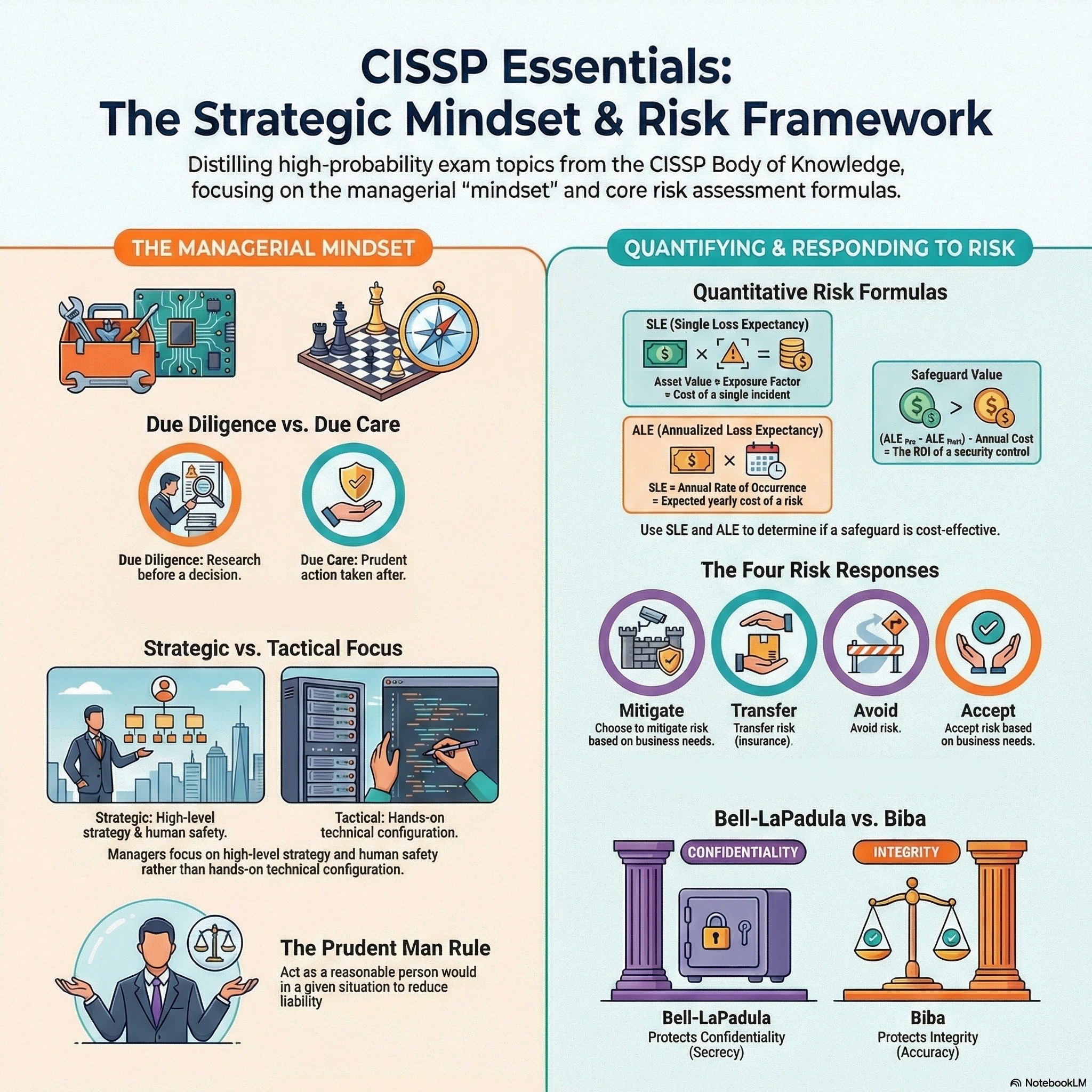
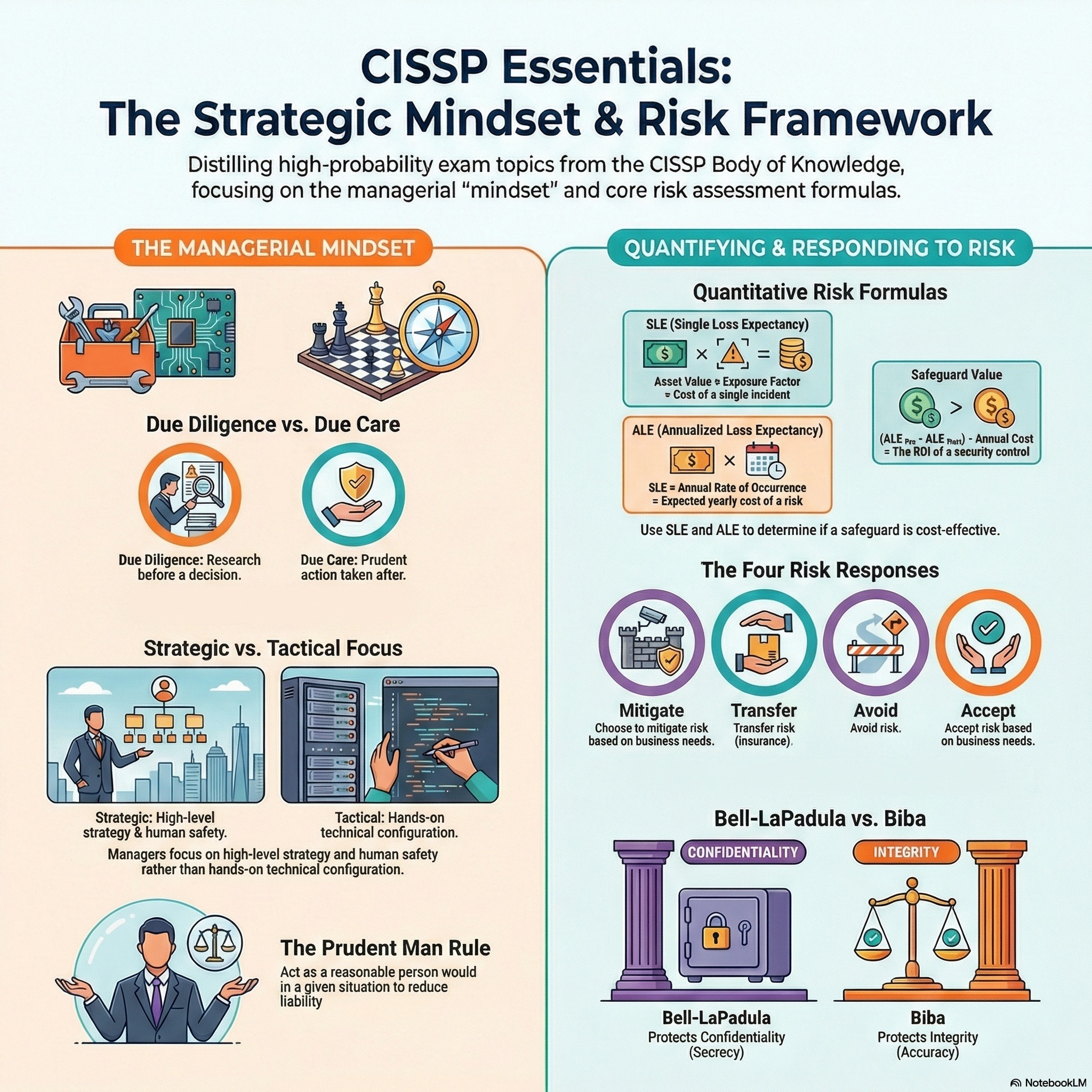
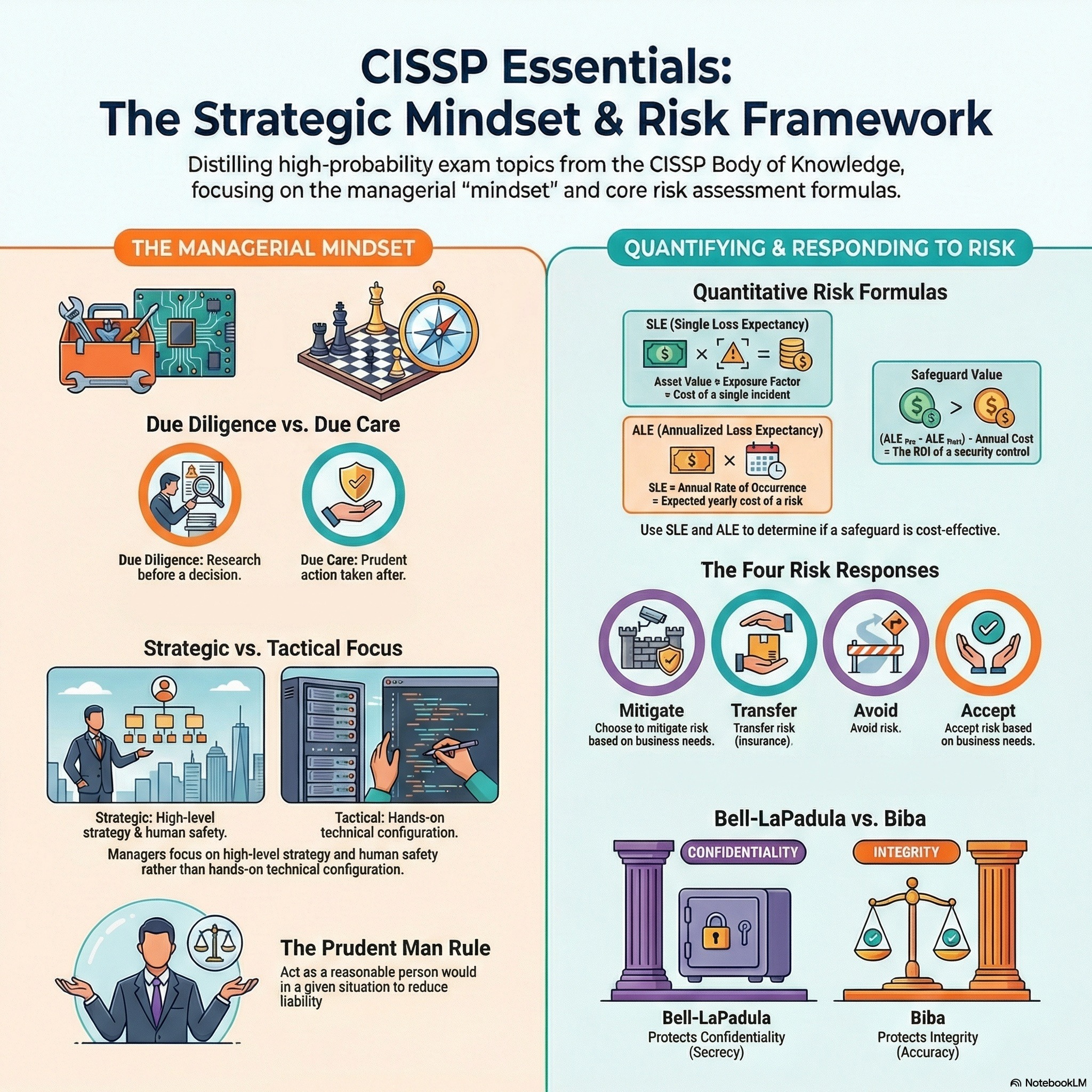
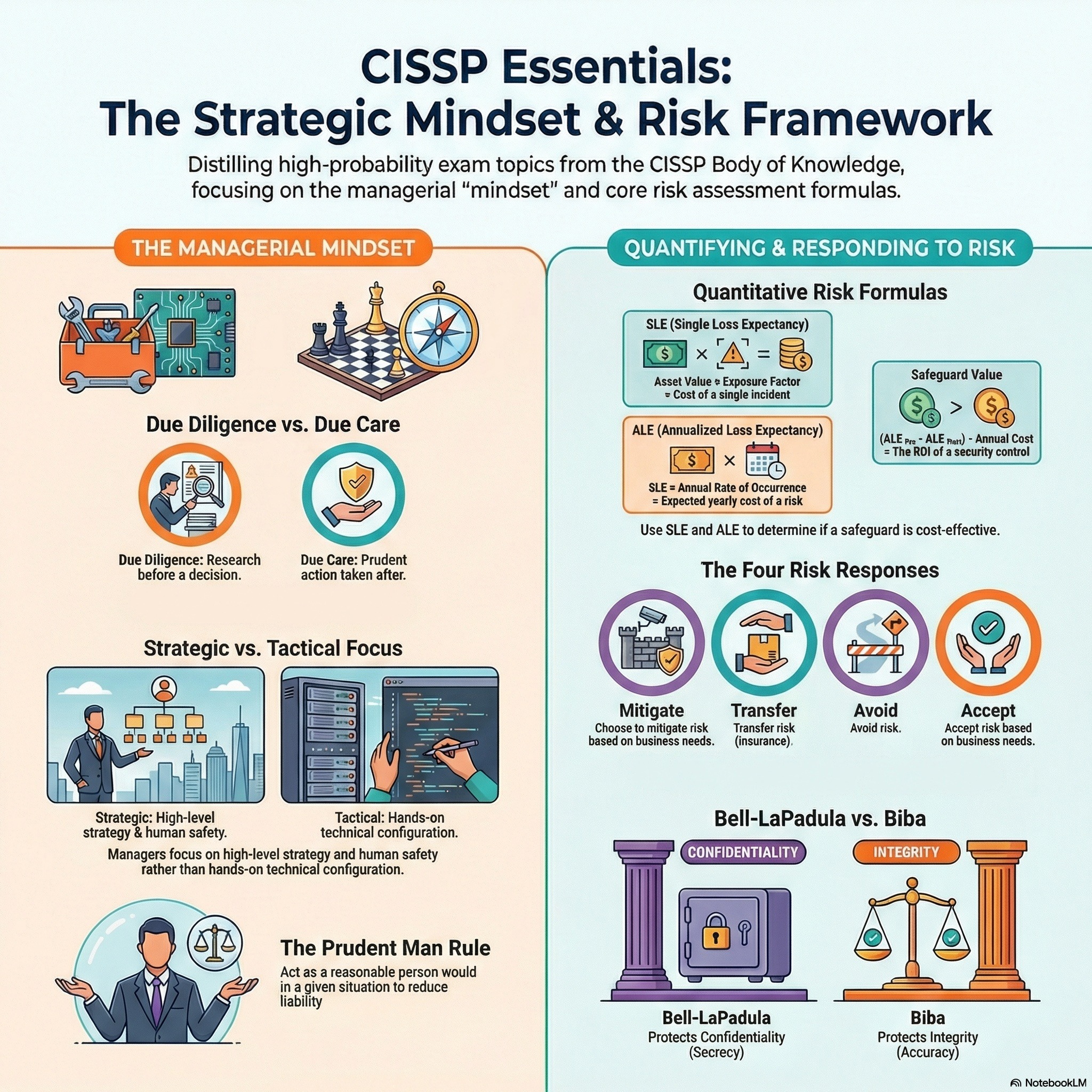
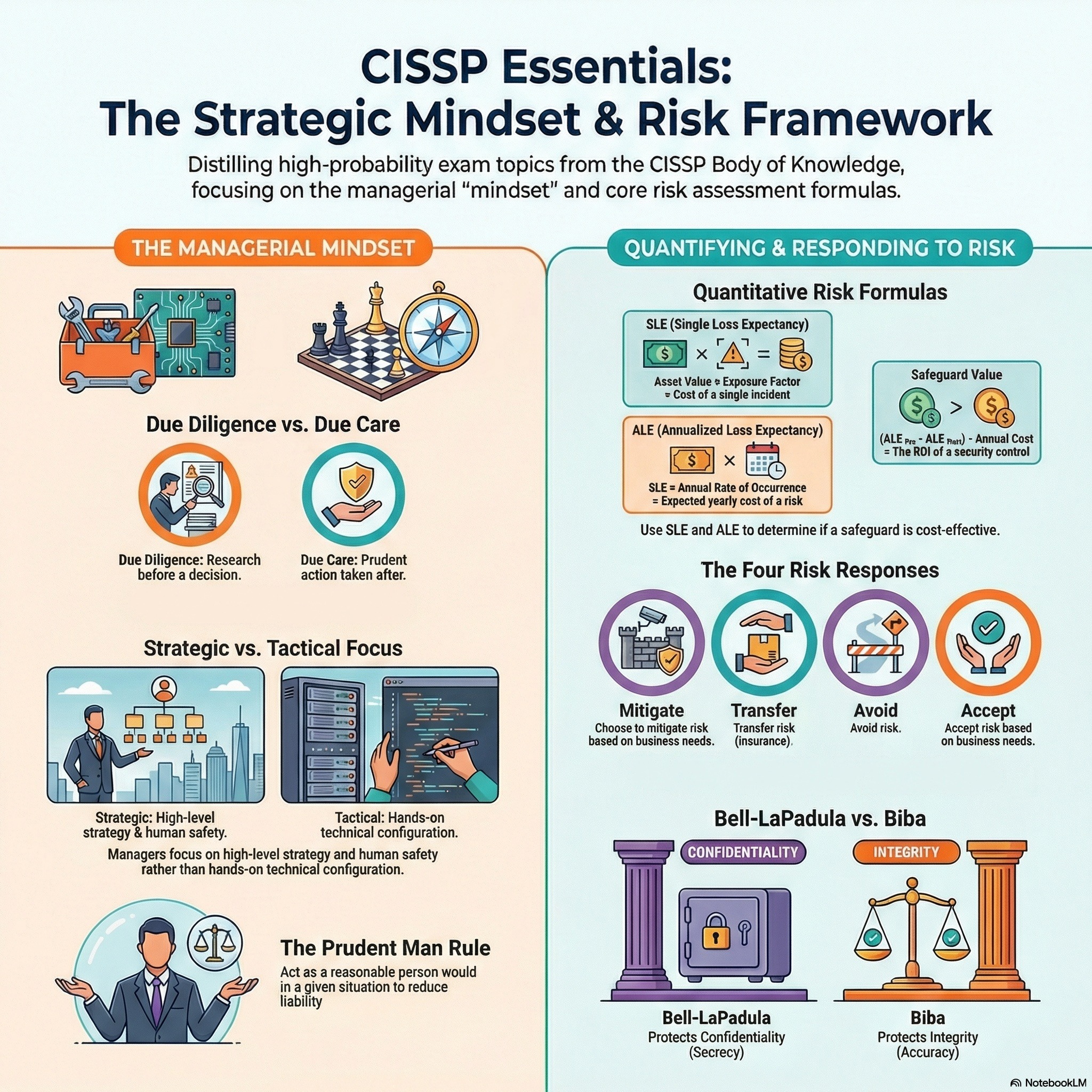
CISSP - Passing CISSP - Think Like a Manager
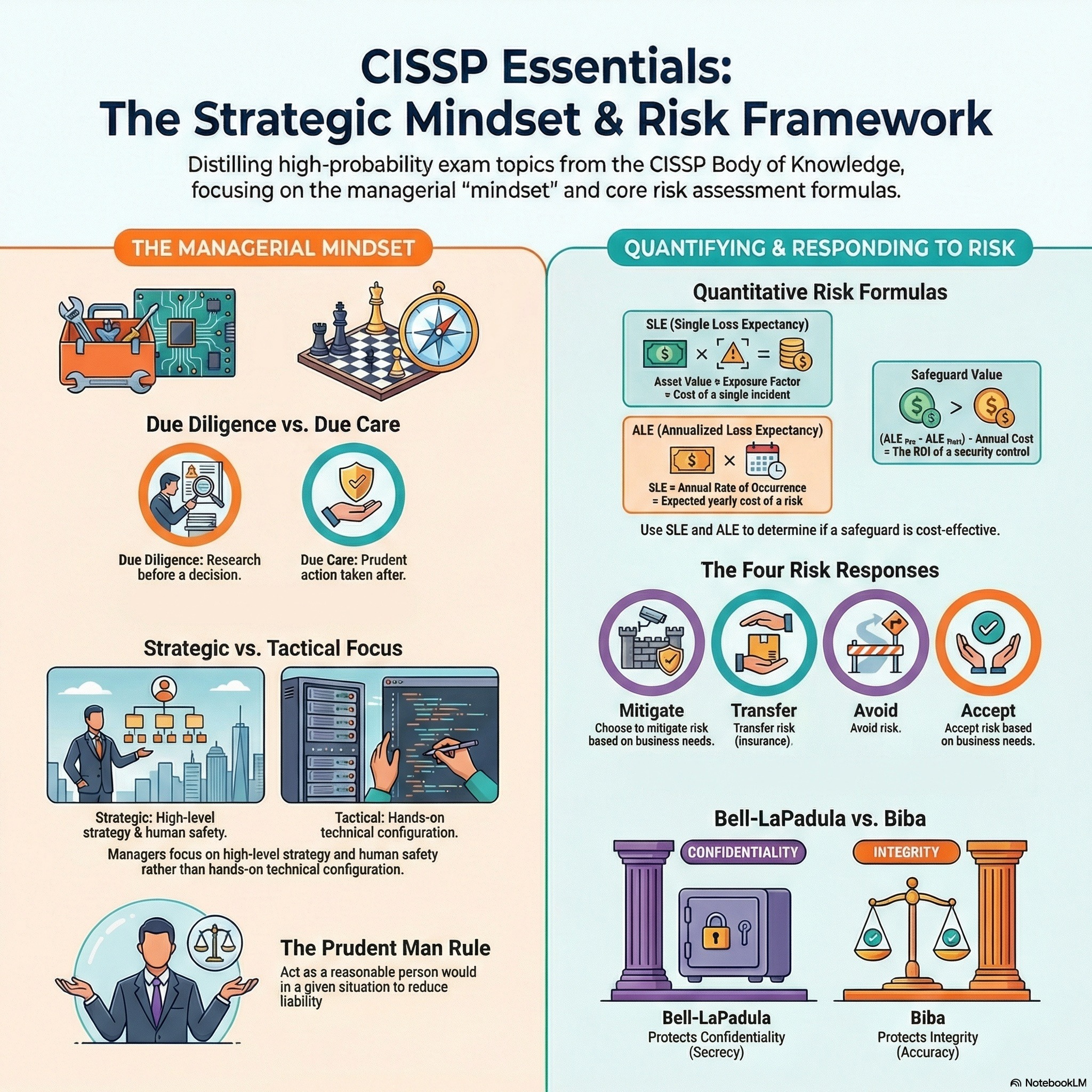
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This podcast focuses on passing the CISSP through proper thinking and approaches.
CISSP - CISSP Mastery - A Manager Mindset
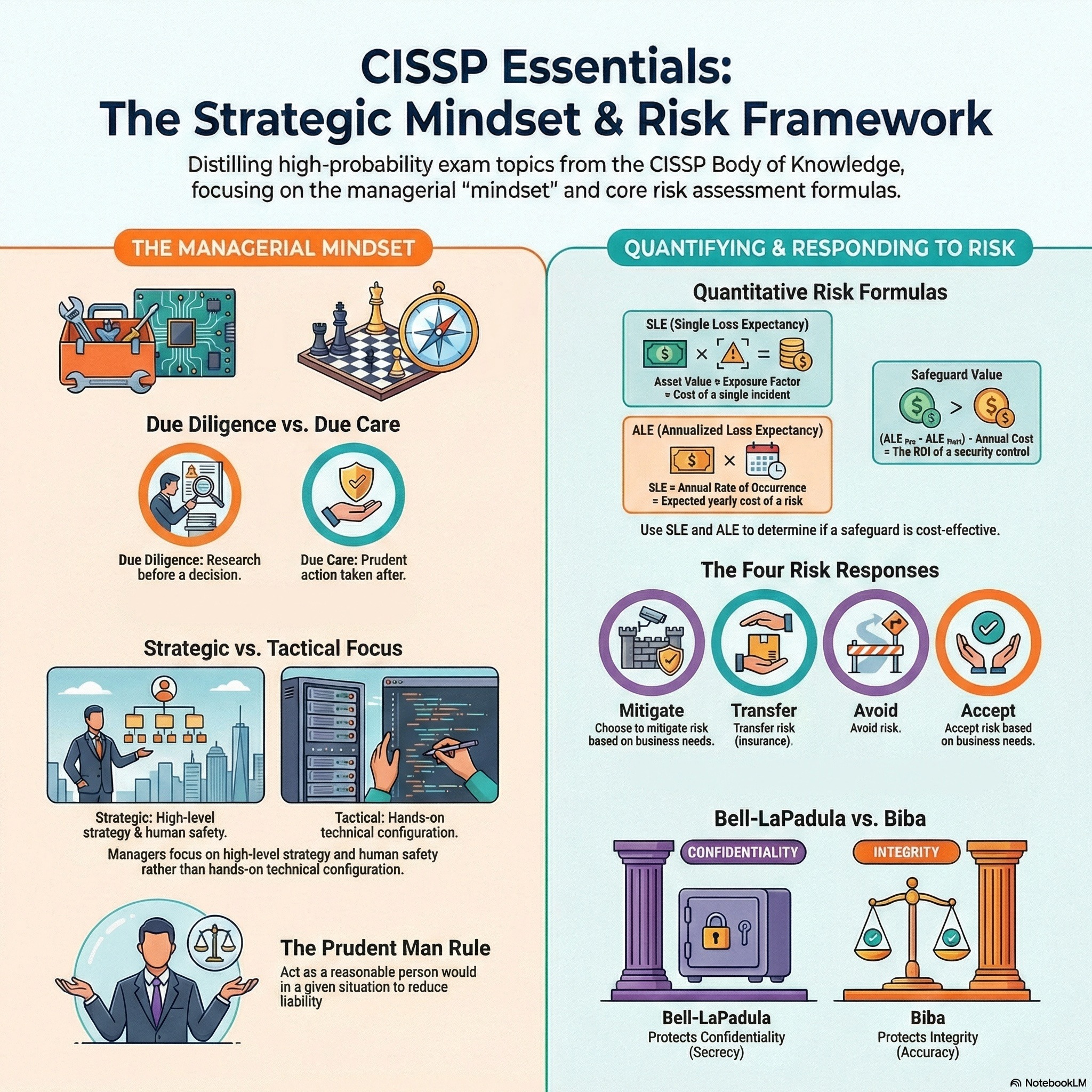
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This podcast focuses on how to think like a manager to master the CISSP.
CISSP - Domain 8 - Secure SDLC, Database Models, and Malware
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This podcast focuses on Domain 8, Secure SDLC, Database Models, and Malware.
CISSP - Domain 7 - Security Operations, Human Safety and the Rest
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This podcast focuses on Domain 7, Security Operations, Human Safety, and the Rest.
CISSP - Domain 6 - Security Assessment and Testing
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This podcast focuses on Domain 6, Security Assessment and Testing.
CISSP - Domain 5 - Identity and Access Management
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This podcast focuses on Domain 5, Identity and Access Management.
CISSP - Domain 4 - Communication and Network Security
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This podcast focuses on Domain 4, Communication and Network Security.
CISSP - Domain 3 - Mastering CISSP Security Models and Cryptography
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This podcast focuses on Domain 3 of CISSP, Security Models and Cryptography.
CISSP - Domain 2 - Asset Management
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This episode focuses on Domain 2 of the CISSP, Asset Management.
CISSP - Domain 1 - Governance & Risk Management
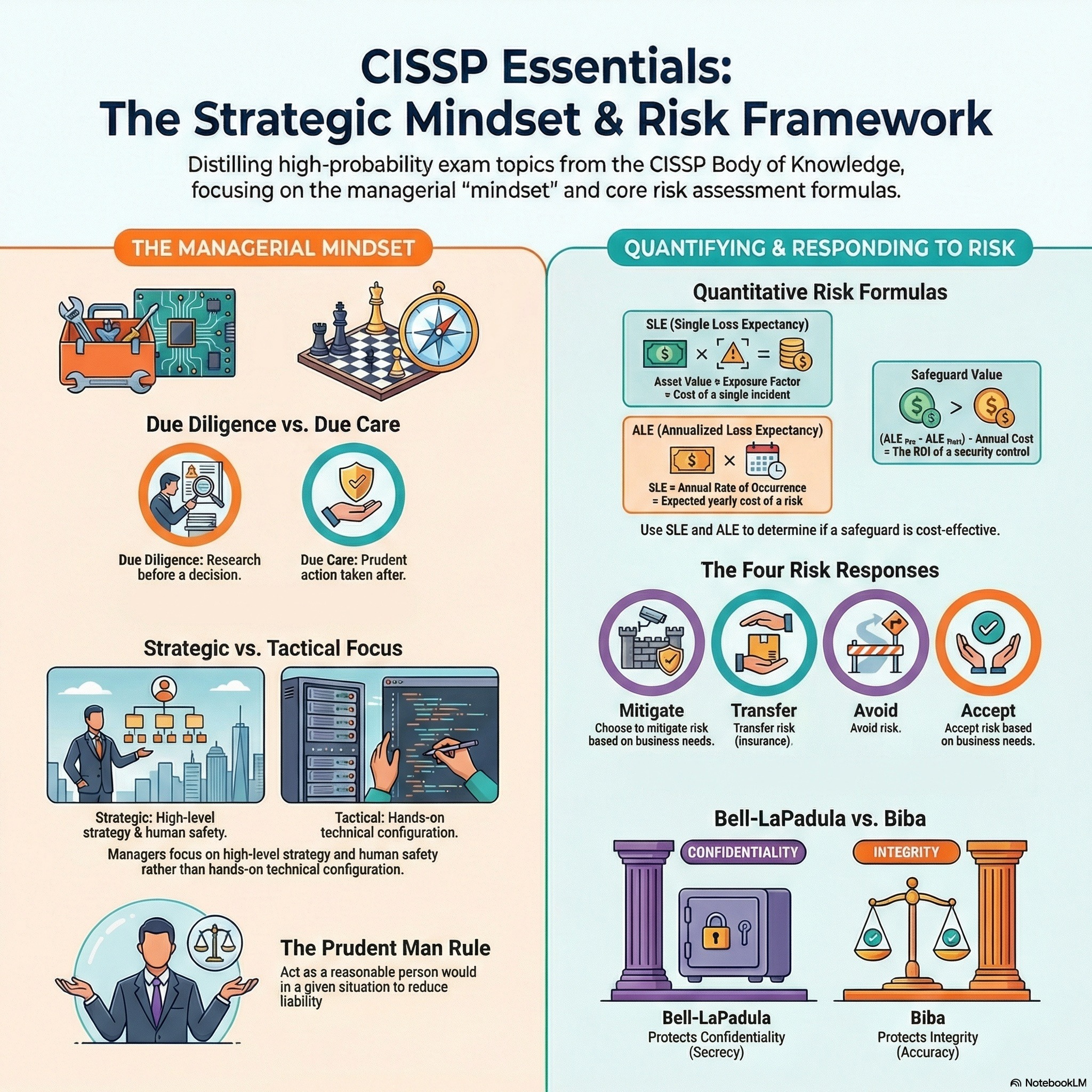
The CISSP exam focuses on risk management, requiring a managerial mindset to align security with business goals. Key concepts include Due Care (action) versus Due Diligence (research), the CIA triad, and the OSI model. Human life is always the top priority. This episode focuses on Domain 1 of the CISSP, Governance and Risk Management.
Security Analytics - Podcast 03 - Fraud, Biometrics, & Bots
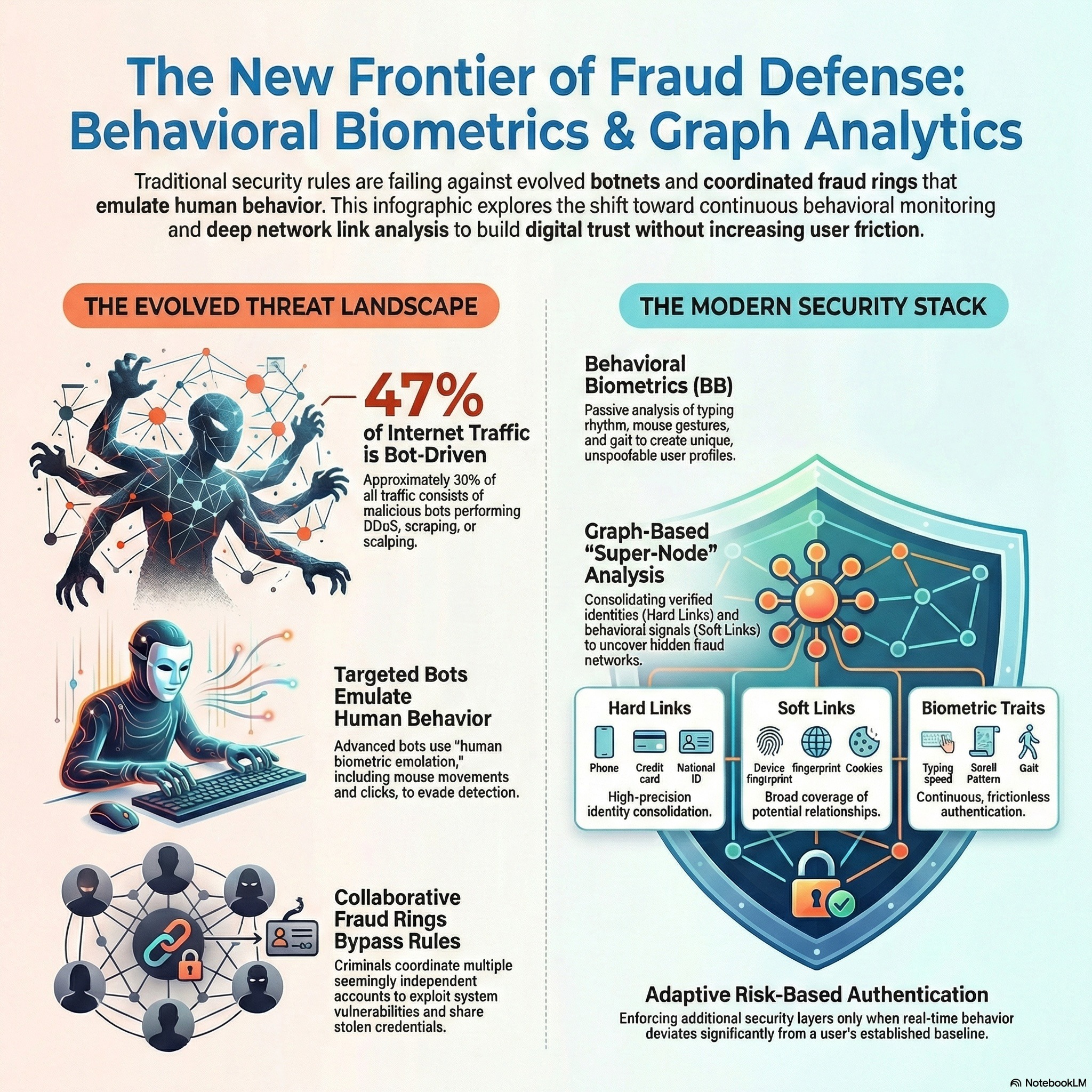
Modern cybersecurity faces sophisticated threats like botnets, insider attacks, and fraud. Organizations utilize Behavioral Biometrics and UEBA to establish baseline user profiles. By analyzing unique patterns like keystroke dynamics, these systems enable real-time defense.
Ethics & Privacy - Podcast 04 - Leasing Privacy From Tech
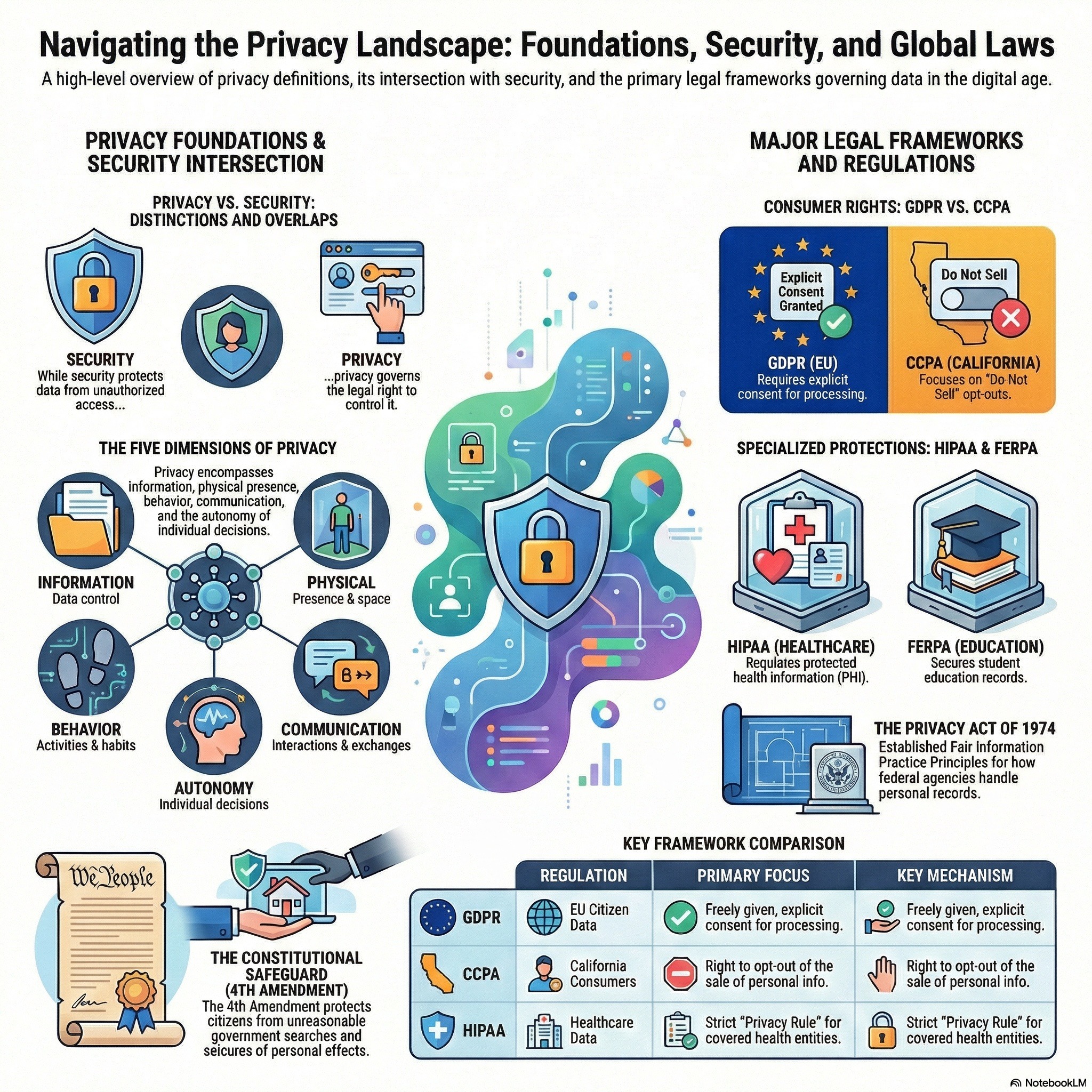
This presentation by Dr. Z defines privacy as a fundamental right. It categorizes privacy into data, physical, behavioral, communication, and decision types. The text also examines the links between privacy and security and legal regulations.